Blockchain attack types
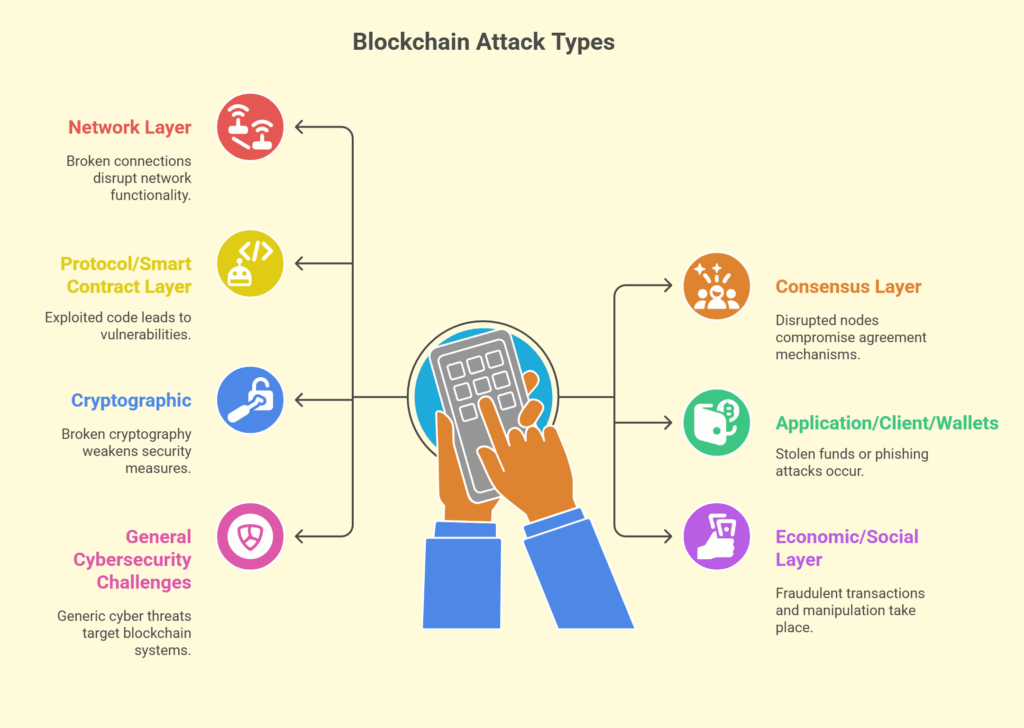
A structured classification method for classifying different kinds of attacks that could jeopardize the availability, security, or integrity of blockchain systems is known as a taxonomy of blockchain attacks. Because they make it easier to find vulnerabilities, examine attack trends, and create efficient mitigation plans, these taxonomies are crucial resources for academics and practitioners.
Blockchain attacks are frequently categorized according to the layer of the blockchain ecosystem they target. In order to classify attacks according to elements like the attack vector (method), the particular vulnerability exploited, the impact of the attack (e.g., financial loss, data breach, disruption), and the impacted layer of the system, taxonomies sometimes adopt a hierarchical or tree-like structure.
Also Read About How Oracle Manipulation Attacks Works: Understanding Threat
The following is a thorough classification of blockchain attacks:
Network Layer Attacks
These attacks take use of blockchain networks’ peer-to-peer (P2P) communication mechanism, which can isolate nodes and impede information flow.
- Eclipse Attack: By controlling all of a node’s connections and providing it with misleading information, an attacker isolates that node from the rest of the network. Other attacks, such as double-spending, may come before this.
- Sybil Attack: To obtain an excessive degree of control over the network, the attacker fabricates a large number of phoney identities (nodes), which can be used to isolate trustworthy nodes or influence consensus. This is expensive in Proof-of-Work systems, and permissioned blockchains can forbid it through background checks.
- Routing Attack (BGP Hijack): By altering internet infrastructure (such as the Border Gateway Protocol), traffic is redirected through rogue nodes, which can delay block propagation and enable double-spending.
- Distributed Denial of Service (DDoS) or Denial-of-Service (DoS): An attacker uses bots to flood a network or node with requests, preventing it from executing transactions and allowing genuine communication. In contrast to centralized systems, the distributed structure of blockchain can assist prevent denial-of-service attacks; however, exchanges have been subject to such attacks, and transactions that have not yet been broadcast in a block are still susceptible.
Consensus Layer Attacks
In order to change or undermine the ledger, these attacks target the consensus mechanism (like as Proof of Work or Proof of Stake) that guarantees that all participants agree on the current state of the blockchain.
51% Attack (Majority Attack)
When an attacker or group gains control of more than 50% of the network’s computing power (also known as hash power in Proof-of-Work systems or staking power in Proof-of-Stake systems), this is known as a 51% Attack (Majority Attack).
This majority allows them to:
- Exceed the rate at which honest miners create blocks.
- Stop the confirmation of new transactions. They are able to reverse their own transactions, which allows them to spend the same digital asset twice.
- Stop the network in effect. Due to the significant expense of obtaining such power, this attack is typically economically unfeasible for large networks; however, it is more possible on smaller blockchains.
- Hard forks to undo harm or permissioned blockchains that take away privileges from non-cooperating nodes are examples of mitigation.
Also Read About Finney attack In Blockchain And How Does Finney Attack Works
Selfish Mining / Shadow Mining:
Shadow mining, also known as selfish mining, is when a miner or group mines a private chain of blocks covertly and without publishing them. By releasing their private chain when it surpasses the public chain, they are essentially “stealing” block rewards from trustworthy miners and undermining integrity.
Nothing-at-Stake Attack
Particular to Proof-of-Stake systems, validators may cast votes on several opposing forks because there isn’t a substantial stake involved, which might cause chain instability.
Long-Range Attack
Attackers try to alter the blockchain from a far-off point in the past, particularly with PoS.
Block Withholding Attack
In an effort to undermine a mining pool and centralize mining power, an attacker joins the pool, helps find blocks, and then withholds the blocks they find rather than sharing them with the pool.
Censoring Transactions
An attacker can prevent particular transactions from being included to the blockchain by gaining a majority of the hash power.
Race Attack
An attacker tries to quickly deliver the same coin to several vendors. If vendors wait for block confirmation, this can be lessened.
Single-Shard-Takeover Attack
This is a problem with sharded blockchains because a single shard can be controlled by a much smaller number of nodes, leaving it open to a majority attack on a smaller scale.
Attacks at the Protocol Layer and Smart Contract Layer
These attacks target errors in smart contract code, transaction regulations, or blockchain logic. Here, coding mistakes and logical fallacies are frequently the source of vulnerabilities.
- Transaction malleability, which can cause confusion in transaction monitoring, is the ability to change a transaction’s ID without changing its content.
- Timejacking: Changing a node’s system time to influence mining difficulty or block acceptance.
- Replay attacks, which occur frequently in post-fork contexts when replay protection mechanisms are not in place, involve reusing a legitimate transaction from one chain in another.
- Smart Contract Exploits:
Reentrancy Attack: Before the first execution is finished, a malicious smart contract repeatedly calls back into a vulnerable contract, consuming money. This was demonstrated by the well-known DAO breach in 2016.
Integer Overflow/Underflow: When an arithmetic operation yields a number that is greater than the utmost or less than the smallest value that a fixed-size integer may contain, it might cause unexpected behaviour, inaccurate computations, or give hackers access to money.
Unchecked Call Return Value: This allows for unexpected behaviour or exploits when an external call’s return value is not verified.
Front-running: To manipulate token values or take advantage of arbitrage opportunities, an attacker watches a pending transaction (particularly in DeFi) and makes a fresh transaction with a larger gas fee to get it verified first.
Timestamp Dependence: The logic of a smart contract depends on the timestamp of the block, which a miner can change to their benefit.
Common Vulnerabilities in Recently Coded Applications: Hasty implementation of new dApps or smart contracts may include new or existing vulnerabilities that can be exploited in a manner similar to those of conventional applications.
Application Layer / Client Layer / Wallets Attacks
Wallets, exchanges, decentralized apps (dApps), or user-facing software that communicates with the blockchain are all specifically targeted by these attacks.
- Phishing attacks involve tricking users into disclosing private keys or wallet login information through social engineering or misleading communications.
- Malevolent dApps: Decentralized programs created to fool users into signing nefarious contracts.
- API Exploits: Abusing flaws in the APIs that wallets or exchanges employ.
- Private Key Theft/Wallet Attack: Using a variety of techniques (malware, insecure storage, brute force, dictionary attacks, SIM swapping, etc.) to obtain unauthorized access to a user’s private key in order to sign transactions and steal related funds, which are typically irretrievably lost because of the immutability of blockchain technology.
- Wallet Vulnerabilities: Defects in a cryptocurrency wallet’s programming that could be used to steal user money.
- Malware Attacks: In order to obtain information or take control of wallets, users’ devices are compromised.
Cryptographic Attacks
These take use of flaws in the cryptographic methods that support the security of blockchains.
- Brute Force Attack: Trying every conceivable combination to guess passwords or private keys.
- Preimage and Collision Attacks: These attacks target hash functions to identify inputs that result in identical outputs, thus jeopardising the uniqueness or integrity of data.
- Quantum Attacks: A possible future danger in which elliptic curve cryptography, which is essential to blockchain security, is cracked via quantum computers.
Economic and Social Layer Attacks
These take use of incentives or user behaviour in the blockchain ecosystem.
- Pump and Dump Schemes: These include increasing token values artificially in order to take advantage of unsuspecting investors.
- Rug Pulls: When developers withdraw user funds from a project, they frequently do it by depleting liquidity pools.
- Governance Attacks: Using a majority vote to advance nefarious ideas in DAO (Decentralised Autonomous Organisation) systems.
Broader Misuse and General Cybersecurity Challenges
The nature of blockchain technology presents broader issues and the possibility of abuse beyond particular attack vectors.
- Misuse for Illicit Activities: “Unsavoury characters” may use public blockchains’ pseudonymity to launder money, making it challenging for law enforcement to track down funds.
- Developer Data Falsification: Developers of blockchain-based systems may, under some circumstances, fabricate data on blockchains.
- Privacy and Traceability Issues: If users’ permissions to view or write data don’t adhere to anonymity or consensus procedures, they may be traceable.
- Malevolent Activities by Permissioned Network Administrators: In contrast to permissionless networks, permissioned blockchain administrators have the ability to take over block production, alter history, or double-spend.
- Lack of Standardisation: This might result in interoperability problems that have an indirect impact on security by preventing dissimilar systems from communicating.
Also Read About Types Of Phishing Attacks & How To Prevent Phishing Attacks
Essentially, the security of a blockchain is only as strong as its weakest link, which includes the implementation of surrounding applications and participant integrity, even while it is strong at its core thanks to encryption and distributed consensus. It is comparable to a multi-layered, intricate fortress: although the core foundations (distributed consensus) and outer walls (cryptography) are extremely strong, attackers will carefully look for any faulty door (smart contract flaws), unsealed window (network vulnerabilities), or bribed guard (social engineering) to get in and compromise the treasury.
