We covered all aspects of brute force attack’s in this blog, including their definition, types, hardware, and tools. Brute Force in Cryptography and Blockchain, Reasons and Repercussions, Online vs offline Password attacks.
Brute force attack meaning
Brute force attack meaning
A brute force attack is a type of cybersecurity attack in which all potential character, number, and symbol combinations are methodically tried until the right one is discovered. It’s frequently referred to as a trial-and-error method. Instead of using cunning techniques or quick cuts, “brute force” refers to the method’s dependence on time and processing power to exhaust all viable alternatives. It’s similar to laboriously attempting every possible number sequence for a combination lock until it clicks , or trying every key on a keychain until the lock unlocks.
How Brute Force Attacks Work
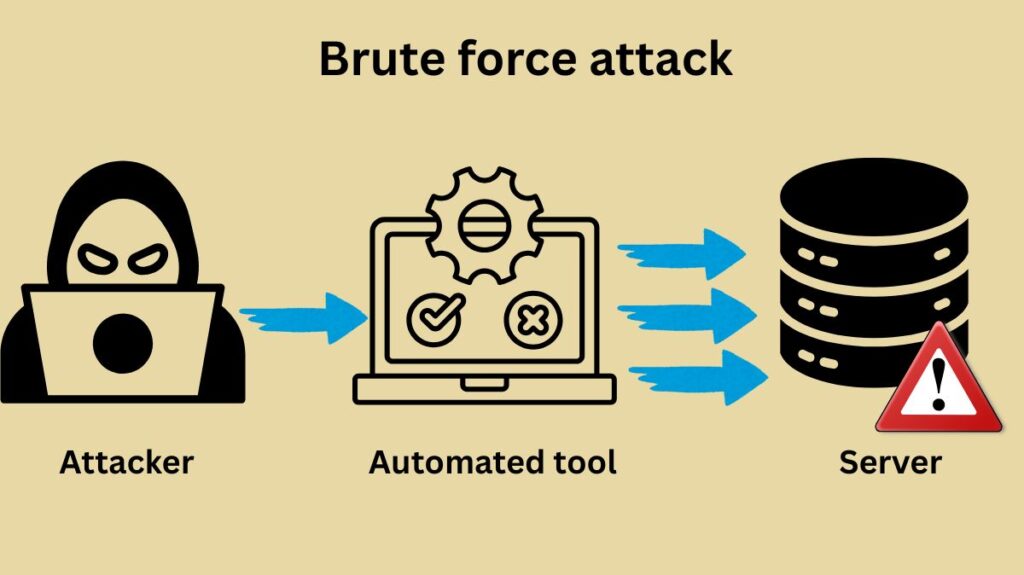
Usually, the procedure consists of the following steps:
- Target Selection: The attacker selects a target, which could be a Wi-Fi network, a locked file, an encrypted system, or an online account (such as email, social media, or banking).
- Guessing Mechanism: The attacker generates and tests a large number of possible passwords, PINs, or keys using automated software or scripts. The majority of contemporary brute force attacks are executed by bots, while some attackers may attempt them manually.
- Systematic Approach: The program adheres to a preset pattern, which may include combining all possible characters in a methodical manner or beginning with single-character passwords, followed by two-character ones, and so forth. Try “aaaaaaa,” then “aaaaaab,” for example, until you get the right combination.
- Verification: The target system receives each generated guess. The system will either provide access (success) or deny it (failure) if there’s a login attempt.
- Iteration: Until the right combination is discovered or the attacker gives up, this trial-and-error procedure is repeated again.
Also Read About Avoid Social Engineering Attacks Blockchain: Best Practices
Important Features
- Lack of sophistication Brute force attacks, which only require computing power and perseverance, are fundamentally simple in contrast to attacks that take advantage of software flaws or social engineering.
- Promised to Achieve (Eventually) Given sufficient time and resources, a brute force attack is theoretically guaranteed to identify the correct key if it exists inside the search space.
- Time-consuming, but becoming more and more possible The length of the password and its complexity (a longer, more complex password has a much greater “keyspace,” making it tougher to crack) affect how long it takes. Cracking time is greatly decreased by attackers who can try millions or even billions of permutations per second using powerful computers, Graphics Processing Units (GPUs), or botnets.
- Requiring a lot of resources (for the attacker) Even though the idea is straightforward, a successful brute force attack can demand a large amount of processing power, particularly when used against strong passwords.
Brute Force Attack Types
Brute force attacks come in a variety of forms:
Extensive search or simple brute force attacks:
This method iteratively cycles through all permitted character combinations to try every conceivable password. Using no prior knowledge of the password, a basic brute force assault (also known as exhaustive search) will repeatedly try passwords such as “aaaa…,” “aaab…,” and so forth through “zzzz…,” incorporating either numbers or symbols based on the character set.
A straightforward brute force assault will eventually discover the right credentials through pure trial and error if given enough time. However, if the password is lengthy or complicated, it can take a lot of time.
Dictionary Attacks
Dictionary attacks use a prearranged list of words, usually from a dictionary, to try various password combinations against a login. To eventually guess the right password, the attacker will use a program to attempt various word and phrase combinations. In addition to employing special or unabridged dictionaries, attackers can build passwords by adding special characters and digits to words. Dictionary assaults can also be carried out by attackers using passwords that have been compromised in previous data breaches.
Because so many individuals choose passwords that are just words or phrases, dictionary assaults can be successful. Such passwords are easily guessable by the attacker’s program.
Brute force hybrid attacks
A hybrid assault blends basic brute force techniques with the dictionary attack methodology. Attackers begin by compiling a list of probable base words, after which they surround them with brute force changes. To meet complexity criteria, the word “spring” might be rewritten as “Spring2025!” by adding capital letters, digits, or symbols.”NewYork1993″ or “Spike1234” are two examples.
Brute force attacks in reverse
The hacker flips the conventional attack technique in a reverse brute force attack. They try one password (or a small collection of passwords) against numerous user accounts rather than numerous passwords against a single user.
Also Read About How Phishing Works And How To Recognizing Phishing Attacks
Stuffing credentials
This takes advantage of the widespread user behaviour of reusing credentials by attempting to access lists of stolen username and password pairs from a single data breach across multiple additional services.
Rainbow Table Attacks
The precomputed tables that include the hash values needed to crack passwords are called rainbow tables. Password hashes generated by a number of hashing methods, such as MD5, SHA-1, and NTLM, can be cracked via rainbow table attacks. Without carrying out the computationally demanding procedure of hashing every potential plaintext and comparing the result with the target hash, attackers can rapidly get the associated plaintext for a given hash.
Spraying passwords
Applying a single, popular password to an excessive number of accounts is known as password spraying. Instead of attempting every possible character combination, the attacker in this case attempts a few of popular passwords across numerous accounts. Since many people use the same password for several accounts, password spraying attacks are frequently successful. By attempting a few common passwords across numerous accounts, they provide attackers access to numerous accounts with comparatively little effort.
Attackers can also get around lockout settings that limit the amount of password tries by using this method. This kind of attack typically targets cloud-based applications that use federated authentication and single sign-on (SSO).
RDP Connection Brute Force Attacks
Remote desktop protocol (RDP) connections have become much more popular since many employees have shifted to working from home during the pandemic. Brute force assaults on RDP connections have escalated in tandem with this growth. Attackers can spread laterally throughout the network and introduce malware if they are able to successfully guess the password for a remote RDP connection.
Online vs offline password attack
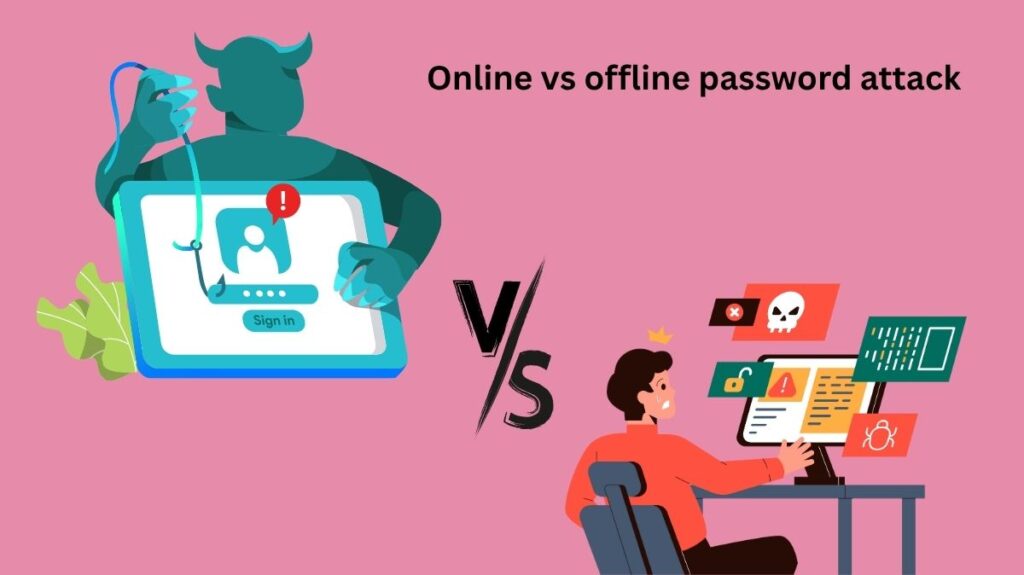
There are two primary situations in which brute force methods can be used:
- Online Attacks: The hacker engages in real-time communication with a live target system, such as an SSH service or website login page. Network latency and defenses like CAPTCHAs and rate limitation restrict the speed of attacks. To avoid detection, attackers frequently employ botnets or spread their attempts across several IP addresses.
- Offline Attacks: Using their own computers, the attacker can make extremely fast guesses without revealing the target system because they have already gotten encrypted data or password hashes (for example, from a data leak). This technique gets around real-time defenses.
Also Read About
| Aspect | Online Password Attack | Offline Password Attack |
|---|---|---|
| Definition | Attacker interacts directly with a live system (e.g., login page) | Attacker works on stolen password hashes or encrypted data locally |
| Target Access | Real-time communication with a system (e.g., SSH, web login) | No direct contact with the system during the attack |
| Speed of Attack | Slower due to rate limits, CAPTCHAs, and latency | Much faster as it’s limited only by hardware performance |
| Detection Risk | Higher – system logs and monitoring tools can detect activity | Lower – no interaction with the live system during guessing |
| Defense Mechanisms | Rate limiting, account lockout, IP blacklisting, CAPTCHA | Strong hashing algorithms (e.g., bcrypt, scrypt), salting |
| Use of Botnets | Often used to bypass IP-based restrictions | Not required; attacker uses their own system |
| Examples | Guessing passwords on a login form, brute-forcing FTP login | Cracking leaked password hashes using tools like Hashcat or John |
| Requires Hash Access? | No | Yes – attacker must have obtained password hashes or encrypted data |
| Resource Intensity | Network and time intensive | CPU/GPU intensive, requires high computing power |
| Success Rate | Generally lower due to defenses | Higher if poor password hashing or weak passwords are used |
Motives and Consequences
Due to frequent vulnerabilities like weak passwords, a lack of rate limiting, and the growing power of contemporary hardware, brute force assaults continue to pose a persistent and potent danger. Hackers carry out these attacks for a variety of nefarious reasons:
- Earnings making money off of advertisements, gathering activity data to sell, stealing identity or personal information, or stealing goods like tax returns and bank accounts.
- Unrest and Malevolent Behaviour distributing malware, taking over systems to create botnets for DDoS or increased attacks, or just creating chaos and problems.
- Damage to Reputation damaging or flooding a website with pornographic material.
- Additional Infiltration Attackers may be able to impersonate users, steal confidential information, or obtain more privileged access within a network as a result of a single stolen account.
Data breaches, monetary losses, the use of computer resources (such as CPU time and bandwidth), reputational harm, a decline in customer trust, and even legal repercussions are just a few of the serious effects that may arise.
Also Read About Types Of Routing Attacks Blockchain And How Does It Works
Hardware and Tools
Almost invariably, brute force attacks are automated. Hackers expedite the guessing process by utilising specialised software tools. These tools can decode encrypted storage, generate any password, find weak passwords, and even translate sentences into “leetspeak” while working with a variety of computer protocols (such as FTP and MySQL). Among the most often used tools are DaveGrohl, Ncrack, Hashcat, Hydra, John the Ripper, L0phtCrack, and Aircrack-ng.
Because of the enormous amount of processing power needed, hackers turn to hardware solutions. Computing power is greatly increased by combining a central processing unit (CPU) with a graphics processing unit (GPU). Password cracking can be hundreds of times faster with GPUs than with a CPU alone because of their thousands of cores, which allow systems to tackle several tasks at once. For example, a single powerful GPU card can solve a six-character password using digits in 3.5 days, but a powerful CPU can take almost two years.
Brute Force in Blockchain and Cryptography
- Cracking Cryptographic Passwords and Keys: Brute force is used to guess private keys or decrypt hashes. Attackers attempt every possible combination of input data for one-way hash functions and see if the hash produced matches the target.
- Bitcoin Private Keys: Even with enormous processing power, brute-forcing these is nearly hard because of their 256-bit size (2^256 combinations).
- Mining as Brute Force: Bitcoin mining is referred to as a brute force technique. Miners iteratively increase a “nonce” and hash it using block header information until the final hash falls below a certain threshold. The computing power needed to solve this puzzle is enormous.
- Cryptography defences: algorithms such as Advanced Encryption Standard (AES) and SCrypt are made to withstand brute force attacks. Brute force attacks against “brain wallets” can also be slowed down using strategies like key stretching.
Future Points to Remember
Since quantum computers might break sophisticated keys (like 2048-bit RSA) in hours as opposed to billions of years, there is worry that the development of these machines could expose existing cryptography keys to brute force attacks. This calls for post-quantum cryptography to be developed.
Essentially, a brute force attack is similar to painstakingly going through each and every piece of hay in an attempt to find a needle in a haystack. Its effectiveness is solely dependent on the size of the haystack and the speed of your investigation, but it is assured to find the needle eventually.
Also Read About What Is 51 Attack In Blockchain And 51 Attack Examples
