Roles in PostgreSQL
Roles in PostgreSQL are essential components for controlling database access privileges and permissions. In order to simplify permission management, PostgreSQL versions 8.1 and beyond adopted a design that incorporates both database users and groups of users into a single, cohesive notion. You can set up a role to behave like a group, an individual user, or both.
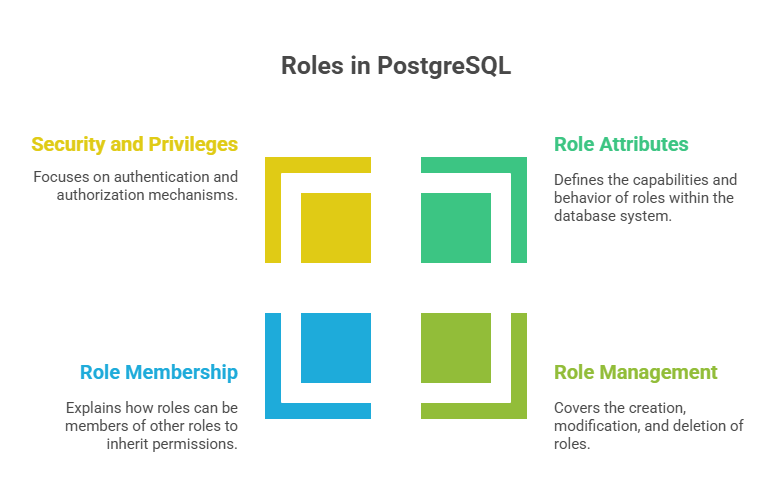
Role Attributes in PostgreSQL
To specify a role’s capabilities and behaviour within the PostgreSQL cluster, it is possible to assign multiple characteristics during the role creation process. A role’s capabilities and interactions with the database system are determined by these attributes:
LOGIN: This property allows a role to establish a connection with the database. Usually used to handle permissions for a group of other roles, roles lacking this property operate as group roles. The CREATE ROLE command with the LOGIN option is the same as the CREATE USER command.
PASSWORD: The password for roles that allow login is specified by PASSWORD. It is advised to set passwords using the \password psql meta-command since it keeps the password from showing up in plain text in server logs or psql history. The pg_shadow catalogue relation by default encrypts passwords.
SUPERUSER: A role that is a superuser can get beyond all permission checks, save for the LOGIN attribute. A superuser role is the first one created during installation for PostgreSQL. For everyday duties, it is recommended practice to avoid acting as a superuser.
CREATEDB: New databases can be created by a role using CREATEDB. Cloned from a template database, such as template1, is any new database.
CREATEROLE:The PostgreSQL CREATEROLE privilege lets a role generate new roles. CREATEROLE users have limited powers, unlike superusers, who circumvent all permission checks. CREATEROLE roles can change and drop other roles if they have ADMIN access. This includes ALTER ROLE (password modifications) and COMMENT and SECURITY LABEL commands.
CONNECTION LIMIT: A user’s maximum number of concurrent connections is defined by the CONNECTION LIMIT. It is advised to manage connections and save by using connection pooling tools or APIs.
VALID UNTIL: This sets the password for the role’s expiration date, after which it loses its validity. With infinity as the default, there is no expiration.
INHERIT / NOINHERIT: Indicates whether a role inherits fellow roles’ rights. Backward compatibility is INHERIT by default. However, superuser permissions are never transferred.
NOLOGIN: PostgreSQL roles that have the NOLOGIN attribute indicate that a client cannot use the role to connect to a database. Because of this feature, the role operates similarly to a database group.
Role Management
Creation: Create roles using the createuser command-line utility or the CREATE ROLE SQL query. Createuser lets you specify whether the user can create databases or other users.
Modification: Changes in PostgreSQL and related tools like DBeaver include changing data values and database structures, customising system behaviour, and adding new features. DML commands like INSERT, UPDATE, DELETE, and TRUNCATE modify data. These commands let users add, update, or delete records from tables.
Deletion: You can use the dropuser utility or the DROP ROLE SQL statement to remove roles. Prior to removing a role, all of its belongings must be dropped or transferred to a different owner, and any privileges that have been granted to the role must be withdrawn.
Role Membership and Inheritance
A fundamental component of PostgreSQL’s authorisation system, role membership and inheritance provide flexible database permission management. To bring these ideas together, a role can act as a database user or a database group. The NOLOGIN feature is frequently used to define roles that are meant to function as groups; these roles act as containers for privileges rather than being able to access directly to the database.
The GRANT command, which permits one role to become a member of another, is used to establish membership (e.g., GRANT group_role TO role1). On the other hand, REVOKE can be used to cancel membership. Although circular membership loops are forbidden, roles can even be members of other group roles. The INHERIT property determines how inherited privileges behave:
INHERIT: Member roles automatically inherit the privileges of their parent roles when they use the default INHERIT attribute. Privileges can be provided to a group role (typically a NOLOGIN role) and automatically applied to its members, simplifying permission administration. A role with the NOINHERIT attribute won’t inherit its parent roles’ privileges.
NOINHERIT: Creating a role with NOINHERIT does not give its members the group role’s permissions. A user connecting as NOINHERIT must explicitly execute the SET ROLE command to temporarily assume the parent role’s identity and privileges to use those permissions. Proxy authentication uses this approach to login with a general user and SET ROLES to specialised roles with task-oriented permissions for further protection.
By using the SET ROLE command, a role with NOINHERIT can nevertheless explicitly take on the privileges of a role it belongs to. By temporarily altering the current_user for permission checks, the SET ROLE command gives the session access to the assumed role’s rights. When an application connects with a generic user and then SET ROLEs to more specialised roles with restricted access for particular activities, this is frequently used for proxy authentication.
Some restrictions on inheritance should be noted:
- One significant exception is that member roles never inherit SUPERUSER rights. A member of a superuser group must specifically SET ROLE to that superuser role in order to exercise superuser rights.
- The SET ROLE command is necessary to use other special role properties, such as LOGIN, CREATEDB, and CREATEROLE, which are also not inherited.
- Additionally, the privilege of BYPASSRLS is not inherited.
A newly formed role is automatically returned to the creating user with ADMIN TRUE, SET FALSE, and INHERIT FALSE options when it is created by a non-superuser with CREATEROLE capability. Because special rights on existing roles require the ADMIN OPTION, this enables the CREATEROLE user to administrate the roles they established. This automatic grant can be customised with the createrole_self_grant configuration parameter, giving the creating user the ability to set the ROLE for usability or automatically inherit privileges. Lastly, any memberships that a role held in other groups are instantly cancelled when it is dropped using DROP ROLE; nevertheless, the member roles themselves remain unaffected.
Security and Privileges
The security model of PostgreSQL mostly depends on roles for authorisation (what the user can do) and authentication (who the user is).
Authentication: According to host, database, user, and authentication method (md5, trust, ident, GSSAPI), pg_hba.conf governs authentication.
Authorization: The technique that determines who can do what on different database objects in PostgreSQL is called authorisation. It differs from authentication, which just confirms a user’s identity when they connect to the database; a user still needs to fulfil the required authorisation requirements in order to access or modify data, even after successful authentication using pg_hba.conf.
Predefined Roles: Predefined roles allow users to access shared privileged capabilities without superuser access. Sample programs include pg_read_all_data, pg_monitor, and pg_signal_backend. These positions enhance system monitoring and administrative management.
Conclusion
The unified role system in PostgreSQL unifies group and user ideas into an attribute-driven, adaptable architecture, simplifying database access control. Administrators may fine-tune authentication and authorisation with capabilities like LOGIN, SUPERUSER, CREATEDB, CREATEROLE, inheritance options, and connection limitations. While preset roles offer helpful capabilities without granting complete superuser powers, role membership makes scalable privilege management possible. When combined, these systems provide strong protection, preserve data integrity, and provide effective management in intricate, multi-user settings.
