Phala Network News

What is Phala network?
A decentralized cloud computing platform, the Phala Network places a high priority on secure computing for Web3 applications while maintaining anonymity. With a focus on data confidentiality and integrity, it seeks to close the gap between the decentralized world and conventional centralized cloud services like AWS or Google Cloud. A group of blockchain and cryptography experts founded Phala in 2018 in response to the increasing need for scalability and privacy in decentralized apps.
Phala Network is a trustless cloud computing solution for Web3, the internet of the future. It aims to address the drawbacks of conventional blockchain technologies, especially those related to privacy and performance in cloud environments.
Key Technologies and Architecture
The distinctive design of Phala Network blends hardware-based Trusted Execution Environments (TEEs) with blockchain technology. Blockchain compute performance, security, and confidentiality are guaranteed by this hybrid technique.
The network is made up of various essential parts:
Phala Blockchain
The foundational layer for safe and decentralized transaction processing is the Phala Blockchain. It functions as a parachain within the Polkadot ecosystem, specifically on the Kusama parachain, and is based on Parity’s Substrate technology. For off-chain workers, the blockchain serves as a canonical (encrypted) message queue.
Off-chain Runtime (pRuntime)
Contracts run in the Secure Enclave’s off-chain runtime, also known as pRuntime. It is a dedicated processing layer that improves scalability and efficiency by shifting computationally demanding jobs from the main blockchain to worker nodes.
Pherry
The pRuntime and the Phala blockchain are connected by the pherry, which serves as the Substrate-Enclave bridge relayer. It guarantees that enclave instances are running an unaltered version of pRuntime and that all blockchain transactions are accurately passed to pRuntime. The pRuntime verifies each block and transaction it receives since it does not trust the pherry.
Trusted Execution Environments (TEEs)
Modern CPUs have “black boxes” called Trusted Execution Environments (TEEs), including AMD SEV, NVIDIA GPU TEEs, Intel SGX, and Intel TDX. Code execution and data storage are separated for privacy, security, and performance. Before leaving, the TEE decrypts, processes, and re-encrypts data for privacy. An abstraction layer offered by Phala unifies the security of different TEEs.
Worker Nodes
By using TEE hardware to run a worker node, anyone can provide processing power to the network. Among these nodes are:
- Miner Nodes are the computational workhorses that execute Phat Contracts, run CPUs with TEEs, and respond to computation requests. To take part and receive incentives, they invest PHA tokens.
- Gatekeepers: These nodes help provide end-to-end encryption between users and miner nodes, maintain network availability, and manage cryptographic keys. They also check TEE employees’ software and hardware.
Phat Contracts (also referred to as Fat Contracts)
Phat Contracts, sometimes known as Fat Contracts, are a novel kind of Phala smart contract. Phat Contracts operate off-chain within the secure TEEs of Phala’s worker nodes, in contrast to conventional smart contracts that run on a public blockchain. They can securely query Web2 APIs and external data sources (oracles) over HTTP/HTTPS, handle sensitive data, and perform complex off-chain calculations. They also provide multi-chain compatibility with EVM and Substrate-based blockchains without a bridge. Phat Contracts is being positioned by Phala as the “Execution Layer for Web3 AI” in order to provide private and secure AI agents.
Dstack
Dstack is an open-source TEE SDK that makes it easier to deploy and run TEE workloads by granting access to CPU and GPU TEEs and abstracting hardware maintenance.
Also Read About What Is Tether (USDT)? How To Invest In Tether In Blockchain
Fundamental Ideas and Benefits
Privacy-Preserving Computation
Phala Network’s core principle is privacy-preserving computation. By encrypting data and guaranteeing that only allowed parties can access it, it makes it possible for private smart contracts and data processing to take place in a secure setting. Users can interact with dApps with confidence without worrying about their privacy because sensitive data is kept private and safe.
Scalability
By transferring computing from the chain to off-chain safe workers, Phala solves scalability issues. The scalability and efficiency of the network are increased overall when demanding jobs are delegated to specialised worker nodes.
Verifiable Computation
With Phala, users may safely assign computationally demanding jobs to off-chain workers while guaranteeing the accuracy and integrity of the output. Secure Enclaves (TEEs), which isolate and safeguard Phat Contract execution and produce cryptographic proofs (such as zk-SNARKs) attesting to its accuracy, are used to do this.
Trustless MEV (Miner Extractable Value)
Phala provides a more secure and trustless MEV ecosystem by executing transactions in Secure Enclaves. By keeping sensitive data private and impenetrable, this ensures decentralisation, security, and justice while reducing MEV manipulation and abuse.
Co-Processor Role
Phala Network co-processes blockchains by assigning computationally intensive tasks to off-chain labour. This distributed computing solution scales seamlessly and decreases blockchain strain, speeding up transaction processing and lowering expenses.
Interoperability
Phala, a Polkadot parachain, can communicate with other parachains, Kusama chains, Ethereum, and other blockchains. Multiple blockchains can share data easily.
Strong Security
To prevent unwanted access and thwart attacks, Phala employs excellent security measures that are thorough and proactive. The network’s resiliency is increased by its decentralized structure.
Cost-Effectiveness
Phala offers a cost-effective solution for both individuals and organisations by cutting operational costs by doing away with middlemen and simplifying procedures through its off-chain computation methodology.
AI-Readiness
With auditable procedures and easy access to safe physical machines for AI development, deployment, and operation, Phala is built to be AI-native. Applications for AI and data analysis that need scalable and safe computation are supported.
Also Read About Types of Security Tokens Blockchain, How it works & Benefits
Token PHA
The Phala Network’s native utility and governance token is called PHA. Among its main duties are:
- Staking: To safeguard the network and receive benefits, network users, including worker nodes (miners and gatekeepers), can stake PHA tokens. Additionally, this ownership serves as collateral for moral behaviour. PHA can be assigned by users to stake pools in order to support network security.
- Governance: By casting their votes on ideas pertaining to the creation and management of Phala Network, PHA holders can take part in network governance.
- Transaction Fees: The network’s computing resources, including the execution of Phat Contracts, are funded by PHA.
- Rewards: PHA tokens are given out as rewards to network contributors, including developers, community members, and node operators.
One billion tokens is the maximum amount of PHA that may be produced.
Applications of Phala Network
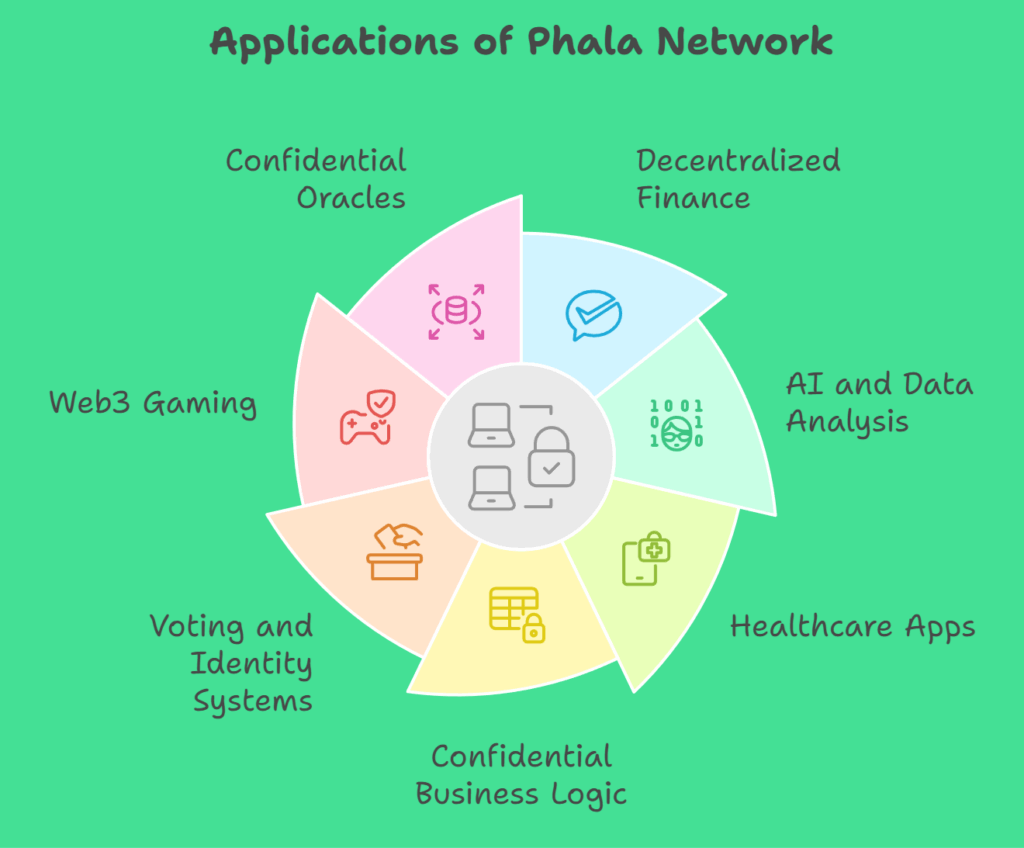
The privacy-preserving features of Phala Network enable a multitude of use cases in numerous industries:
- Enabling privacy-preserving financial services such as private order books, secret lending and borrowing, and safe handling of sensitive financial data is known as decentralized finance, or DeFi.
- Supporting AI and data analysis applications that need scalable and secure computation, enabling companies to handle private information without jeopardising privacy, and securely developing and implementing AI agents are all examples of artificial intelligence (AI) and data analysis.
- Apps for healthcare: safely managing and analysing private patient information.
- Safeguarding proprietary algorithms or trade secrets is known as confidential business logic.
- Voting and identity systems that protect privacy include managing decentralized identifiers (DIDs) with sensitive information and guaranteeing safe and private voting.
- Web3 gaming is the creation of games that protect user information or delicate game logic.
- Confidential Oracles: provide other blockchains with private and reliable data feeds.
Implementing Secure Smart Contracts
There are numerous crucial processes involved in deploying a private smart contract on Phala Network:
- Writing the Contract: The terms and conditions of the contract must be precisely defined because it is written in languages like Solidity or Ink.
- Testing: This important phase runs simulations and collects input for improvement to confirm the contract’s operation in a variety of circumstances.
- Phala Network provides specialised resources and a setting to make contract integration easy while ensuring security and privacy compliance
- Final phase: Verification ensures contract privacy and security by reviewing code, privacy policies, security measures, and legal and regulatory compliance.
Community and Future Prospects
Phala Network uses open-source development and has a GitHub codebase. Fans, developers, and contributors rule and build it.
Enhancing TEE integration, adding new features and use cases for Phat Contracts, encouraging ecosystem growth by onboarding more developers and partners, and bolstering cross-chain interoperability are some of the upcoming projects for Phala Network.
| Feature | Details |
|---|---|
| Type | Privacy-preserving cloud computing & smart contracts |
| Built on | Polkadot (parachain) |
| Launch | Secured a Polkadot parachain slot in 2021 |
| Native Token | PHA |
| Core Technology | TEEs (Trusted Execution Environments) |
| Unique Feature | Confidential smart contracts |
| Purpose | Securely process sensitive data on-chain |
