We talked about UTM Firewall in this blog. The features, advantages, disadvantages, and comparison of UTM Firewall Vs NGFW are all covered below.
Define UTM firewall
An all-in-one security solution that combines several security elements into a single device or service is a Unified Threat Management (UTM) firewall. Simplifying security administration and providing all-encompassing defence against a variety of cyberthreats are its primary objectives. A UTM firewall offers centralized protection as opposed to using separate solutions for different security functions, which makes it especially appropriate for small to medium-sized organisations (SMBs).
Also Read About Advantages and Disadvantages of Ethernet, Wi-Fi VS Ethernet
How does UTM work?
Appliances and functionality make up UTM implementations. Several security elements are stored and combined in UTM appliances. Appliances may consist of applications or actual hardware.
Devices and appliances integrate firewalls and virus scanners as part of Unified Threat Management. They make it possible to update applications and modify configurations. Through application control, control systems also enable security teams to keep an eye on every component.
The distinct parts that make up the security system are UTM functions. Cloud firewall tools, malware scanners, email filters, and specialised data loss protection solutions may be included.
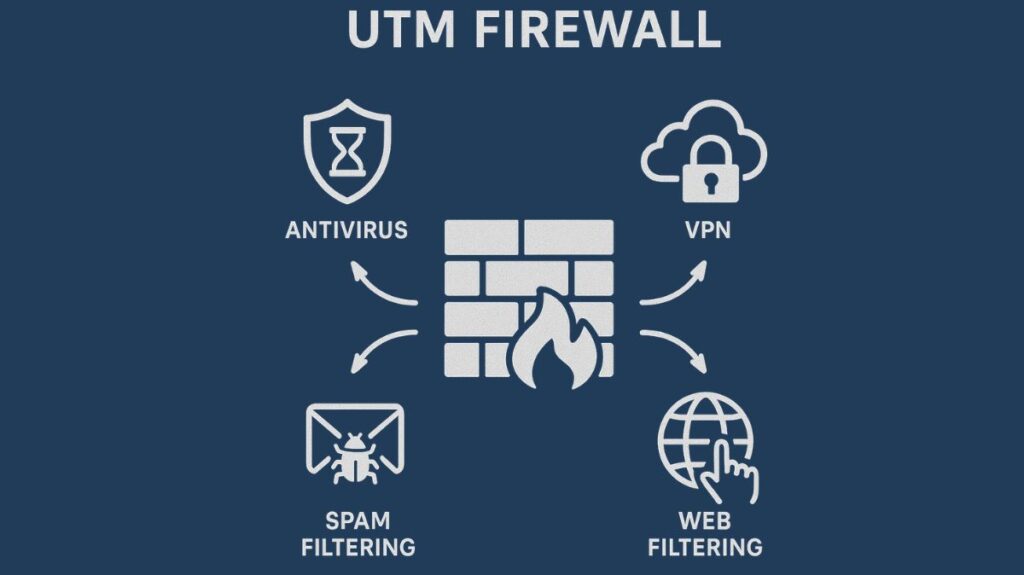
UTM firewall features
Typically included in a UTM firewall are the following essential features:
Traditional Firewall Functions:
Packet filtering, stateful inspection, and network address translation (NAT) are examples of traditional firewall functions. Depending on the status of the connection, a stateful firewall examines network traffic.
Intrusion Detection and Prevention (IDS/IPS)
This function actively monitors network traffic to prevent attacks in real-time and identifies and stops harmful or suspicious activities.
Protection against viruses and malware
It checks traffic for dangers like ransomware, worms, viruses, and other harmful software. This frequently goes by the name of Gateway Antivirus and scans both outgoing and incoming traffic.
Web and Content Filtering
This feature prevents users from accessing certain content categories or URLs as well as dangerous, improper, or malicious websites.
Spam filtering
It prevents unsolicited and harmful emails, shielding clients and email servers from phishing scams, junk mail, and other online dangers.
Support for Virtual Private Networks (VPNs)
This enables site-to-site connectivity or safe, encrypted remote access for staff members.
Advantages
UTM firewalls have a number of advantages.
- Simplicity and Centralized Management: Since all security operations are managed from a single interface, this offers a major advantage in terms of simplicity of management. As a result, managing several different security products becomes less complicated and time-consuming.
- Cost-Effectiveness: UTM firewalls save SMBs money by combining several tools into a single device, which lowers the total cost of ownership, including hardware, licensing, and maintenance.
- Integrated Protection: By ensuring that all security measures function as a single unit, the unified nature helps close security gaps that may occur when employing products from several vendors.
- Broad Protection: They offer all-encompassing defence against a variety of dangers.
Also Read About Importance Of Endpoint Security, Advantages & Disadvantages
Disadvantages
But there are also certain restrictions:
- Performance Impact/Bottleneck: In high-traffic situations, a single device that handles multiple security functions at once may constitute a performance bottleneck. Traffic jams could cause it to slow down.
- Less Specialized: Compared to specialized, standalone security solutions (such a standalone intrusion prevention system), UTM solutions are typically less potent and specialised.
- Single Point of Failure: The network will be totally exposed if the UTM device malfunctions because all of its integrated security features will stop working.
- Limitations on Scalability: Because UTM solutions are mainly developed for SMBs, they might not be scalable enough to satisfy a large enterprise’s performance and functionality needs.
A medium-sized business, for instance, might set up a UTM Firewall at the network edge to use a single device to block malware and phishing emails, stop employees from viewing malicious websites, enable secure Virtual Private Network(VPN) connection for distant workers, and keep an eye on network traffic for unusual activity.
UTM firewall vs NGFW
| Feature/Aspect | Next-Generation Firewall (NGFW) | Unified Threat Management (UTM) |
|---|---|---|
| Primary Focus | Advanced firewall with deep packet inspection, application and user identification, and intrusion prevention | All-in-one security solution integrating multiple security features |
| Functionality | Specializes in firewalling, intrusion prevention (IPS/IDS), application control, and policy enforcement | Combines firewall, antivirus, anti-spam, VPN, web filtering, IDS/IPS, etc. |
| Performance | Higher performance, optimized for enterprise networks | Performance may degrade if too many services are enabled |
| Scalability | Highly scalable for large enterprises and data centers | More suitable for small to medium businesses (SMBs) |
| Complexity | More complex configuration and management | Easier to deploy and manage (single interface) |
| Security Depth | Deeper inspection of traffic, focuses on application-level security | Provides broad but less specialized security |
| Best Suited For | Enterprises needing granular control and advanced security | Small/medium businesses needing cost-effective, simplified security |
Briefly:
NGFW = Enterprises’ deep, specialized, high-performance security
UTM = Comprehensive, easy-to-use, one-stop protection for SMBs
Also Read About What Are Firewall Logs? Benefits And Importance Of Firewalls
