What is Syslog server
A centralized system that may be either software or hardware, a syslog server is made to gather, store, and process system messages (log messages) from different servers, network devices, and applications using the Syslog protocol. By combining logs into one easily accessible area, it acts as a central repository for all digital activities taking place throughout a network, which is essential for keeping an eye on and debugging network occurrences.
A syslog server, to put it simply, is a central log hub that assists network administrators in monitoring all system activity.
What is the Benefits of a Syslog Server
Centralized Logging: Syslog servers make log management easier and user account management more scalable by giving administrators a single point of access to observe all system activities. Because it eliminates the need to log into each device separately, this is the main benefit.
Monitoring and Troubleshooting: In order to diagnose issues and keep an eye on the health of the network, they collect vital logging data. Centralized logs allow managers to swiftly find and pinpoint the source of network or system problems, thereby cutting down on downtime.
Filtering and Searching: Syslog is a strong troubleshooting tool because it lets administrators see, sort, search, and filter messages based on keywords and severity levels.
Reporting and Alerts: Certain syslog servers can even reply to certain system messages by emailing or paging managers in addition to providing reporting features.
Enhanced Security Monitoring: Centralized logs offer a thorough perspective of security-related occurrences, assisting in the identification and analysis of security incidents as well as questionable trends, including repeated unsuccessful login attempts across many systems.
Compliance & Auditing: By providing a central repository for log data and enabling data preservation policies which are essential for audits syslog servers help organizations comply with regulatory frameworks such as HIPAA and PCI-DSS.
Reduced Device Burden: They save the storage space and processing power of individual devices by offloading the responsibility of keeping and storing logs.
Syslog data is frequently sent by routers, switches, firewalls, web servers, Unix/Linux-based systems, application servers, printers, and scanners.
How Syslog Server Works
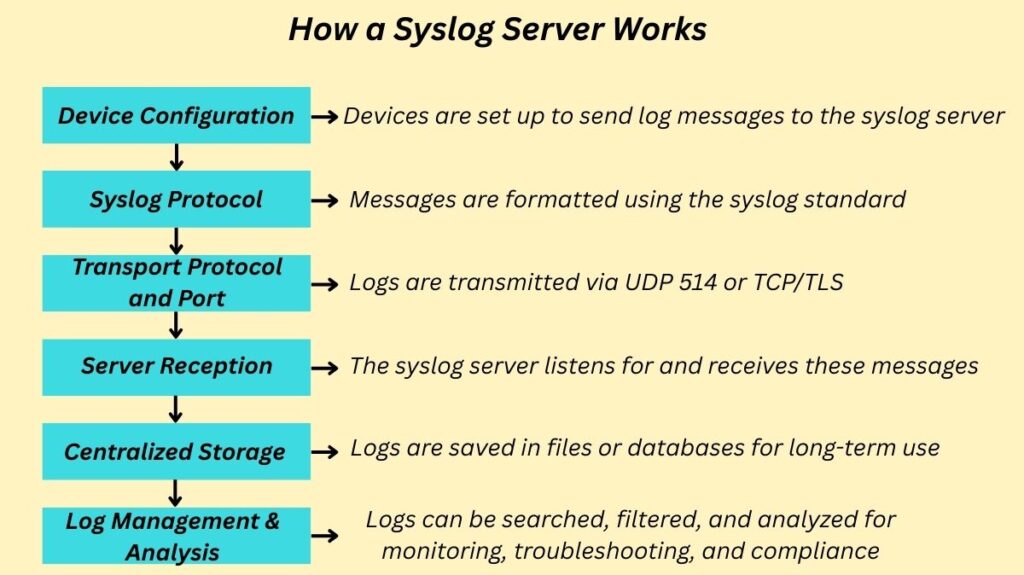
A client-server architecture underpins how a syslog server functions:
Device Configuration: Log messages are generated in a defined format and sent to the IP address of the syslog server by network devices, servers, and applications (syslog clients).
Syslog Protocol: The Syslog protocol is used by these devices to format and send messages. As per the Syslog standard, there are three layers:
- Syslog content layer: Include informative components such as facility codes and severity levels in addition to the event message’s actual contents.
- Syslog Application layer: In charge of the message’s creation, interpretation, routing, and storage.
- Syslog Transport layer: Sends the communication over a network.
Transport Protocol and Port: User Datagram Protocol (UDP) port 514 is the main port that Syslog utilizes to transmit event notification messages across IP networks.
- Unreliable Delivery: Because UDP is a connectionless protocol, syslog messages are not acknowledged and are not sequenced. This might result in a loss of logging information on networks that are frequently utilized since some packets can be lost.
- Reliable Delivery: TCP or TLS encryption is also used by some contemporary implementations and network devices for more dependable delivery.
Server Reception: The collector, also known as the syslog server, watches the assigned network port for incoming messages.
Centralized Storage: In order to facilitate long-term retention and simpler analysis, communications are centrally kept once they are received, such as in log files or a database. For syslog servers to manage the substantial volume of data produced by networks, a sizable database is necessary.
Log Management & Analysis: Tools for viewing, filtering, searching, and analyzing the gathered logs are provided by the server in order to spot problems, keep an eye on security, and satisfy legal obligations.
Syslog Message Format
Specific fields are present in every syslog message and are frequently organized as follows:timestamp: facility-severity-MNEMONIC as a percentageexplanation:
Sequence Number (seq no): Sequence number logging is optional and requires configuration; it is not enabled by default.
Timestamp: The time and date of the event or communication. To correlate events across devices, this is likewise not enabled by default, although it is strongly advised. In particular, for troubleshooting and event correlation, Network Time Protocol (NTP) is essential for synchronizing clocks across all network devices and guaranteeing consistent timestamps. Date and time with milliseconds are included using the service timestamps log datetime msec command.
Facility: System status data is categorized using a service identification that identifies the source of the message (e.g., IP, OSPF, SYS operating system, IPsec, Interface IP). Although this may be altered, local7 (debugging) is normally used by default on Cisco IOS devices. The range of facility codes is 0 (kernel messages) to 23 (local use 0-7).
Severity: The severity of the notification is indicated by a single-digit code (0–7) or keyword, where lower numbers denote more serious occurrences. Administrators may now select which messages are issued according to their level of severity.
Level 0: Emergencies, or situations that make the system inoperable.
Level 1: It is imperative that something be done right now.
Level 2: Is referred to as crucial, and “critical conditions” is the simple explanation.
Level 3: Conditions of errors
Level 4: Circumstances of warning.
Level 5: A “normal but significant condition” is represented by a notice or notification.
Level 6: Messages of information
Level 7: Messages at the debug level
MNEMONIC: A string of text that distinguishes the message.
Description: A string of text with comprehensive details regarding the incident.
Message Size: The size of syslog messages cannot be more than 1024 bytes.
Configuring Syslog on Cisco Devices
Cisco routers and switches are often configured using three global configuration steps in order to deliver logs to a syslog server:
Specify Syslog Server IP Address: Use the logging {ip-address | hostname} command to define the syslog server’s IP address or hostname.
Control Message Levels: Use the logging trap {level-name | level-number} command to set the minimum severity level of messages to be sent. Messages of this level and all more severe levels (lower numbers) will be sent. For example, logging trap warning or logging trap 4 sends messages of severity 4 (warnings) and lower (0-3).
Specify Source Interface (Optional): Use logging source-interface interface-type interface-number to ensure syslog packets contain the IP address of a specific interface, typically a loopback interface for consistency.
Cisco devices can also send log output to other destinations, including the console (default debug level, can be enabled with logging console and synchronised with logging synchronous), an internal RAM buffer (logging buffered), or terminal lines for Telnet and SSH users (logging monitor and terminal monitor commands). Log messages can also be generated as SNMP traps and sent to an SNMP manager.
Syslog Server Configuration for Cisco Meraki Devices
It is possible to set up Cisco Meraki MX Security Appliances, MR Access Points, and MS switches to transmit messages to a syslog server for reporting purposes.
Message Categories/Roles:
- URLs, flows, event logs, and IDS alerts are all supported by MX security appliances.
- IDS alerts are the only alerts sent by MR Access Points.
- Only Event Log messages are now supported by MS switches.
- Messages can include HTTP GET requests (URL), inbound and outbound flows (now often called ‘firewall’ in more recent firmware), appliance, switch, and wireless event logs (e.g., DHCP lease information), security events such as IDS alerts (MX only), and Air Marshal events (e.g., rogue SSIDs).
Dashboard Configuration:
In the Meraki Dashboard, syslog servers are configured under Network-wide > Configure > General (or “Logging” for networks that are appliance-, switch-, or wireless-only). An IP address, a UDP port number, and the roles to send must all be specified. You can set up more than one syslog server. If an MX security appliance’s “Flows” role is active, the Security & SD-WAN > Configure > Firewall page allows you to set or disable logging for certain firewall rules.
Traffic Flow Scenarios:
How an MX device connects to the syslog server determines the source IP of its syslog traffic:
- Via LAN: Communications coming from the server’s VLAN interface.
- Via Public Interface: The public interface is the source of the traffic.
- Via AutoVPN or non-Meraki VPN: An allow rule in the “Site-to-site outbound firewall” could be necessary, and MX utilizes the source IP linked to the highest-numbered VLAN taking part in the VPN.
A syslog server can be easily configured on a Linux system, with syslog-ng being a common application. An example configuration for Ubuntu using syslog-ng would involve installing the application, editing /etc/syslog-ng/syslog-ng.conf to define the syslog source (e.g., udp(ip(192.168.10.241) port(514))), filter by the MX’s host IP, and define destinations for logs (e.g., /var/log/meraki.log for all messages, or separate files for different role categories using regular expressions), and then restarting the syslog-ng process.
Security and Resource Management Considerations
Clear Text Transmission: The fact that syslog messages are usually sent via UDP port 514 in clear text (unencrypted) presents a security concern.
Securing Syslog: It is advised to lock down syslog by allowing this communication only between the defined syslog servers and the IP address of the network device. Security can be improved by encrypting in-band management traffic using IPsec or by using an out-of-band (OOB) management technique (such as a separate VLAN for management traffic). TCP, TLS, and RELP are also supported by certain contemporary syslog systems for more dependable and secure transmission.
Resource Management: A device’s CPU and storage might get overloaded by excessive logging. To prevent performance damage, administrators should choose the right severity levels and log just the information that is required. Particularly “flows,” syslog messages can take up a lot of disc space, therefore the host must have enough storage.
Syslog vs SNMP
Although they are both used for network device monitoring, Syslog and Simple Network Management Protocol (SNMP) function differently. Polling devices are often used by SNMP to gather data, whereas Syslog devices send out notifications when certain criteria are met. Syslog covers a wide range of events and is less format-constrained, but SNMP is frequently most effective in scenarios with predictable conditions. It is common for syslog servers to accept SNMP data, especially SNMP traps.
Syslog Flavours
There are now other “flavours” of the Syslog protocol in addition to the original:
Syslog-ng: Developed in 1988, it differs from the original Syslog in syntax and provides new encryption and filtering features.
Rsyslog: It was created in 2004 and is directly developed from Syslog. It may be used in place of Syslog and supports the usage of a syslog.conf file as rsyslog.conf. Additionally, it has better capabilities for interpreting unstructured data and sending it to other locations. Both rsyslog and syslog-ng can send messages via TCP, TLS, and RELP in addition to UDP.
