Circuit-Level Gateway
A Circuit-Level Gateway (CLG) is a kind of firewall that functions at the Open Systems Interconnection (OSI) model’s session layer, or Layer 5. An alternative name for it is a session firewall. Verifying network sessions to make sure they adhere to security regulations is its main duty.
How It Works
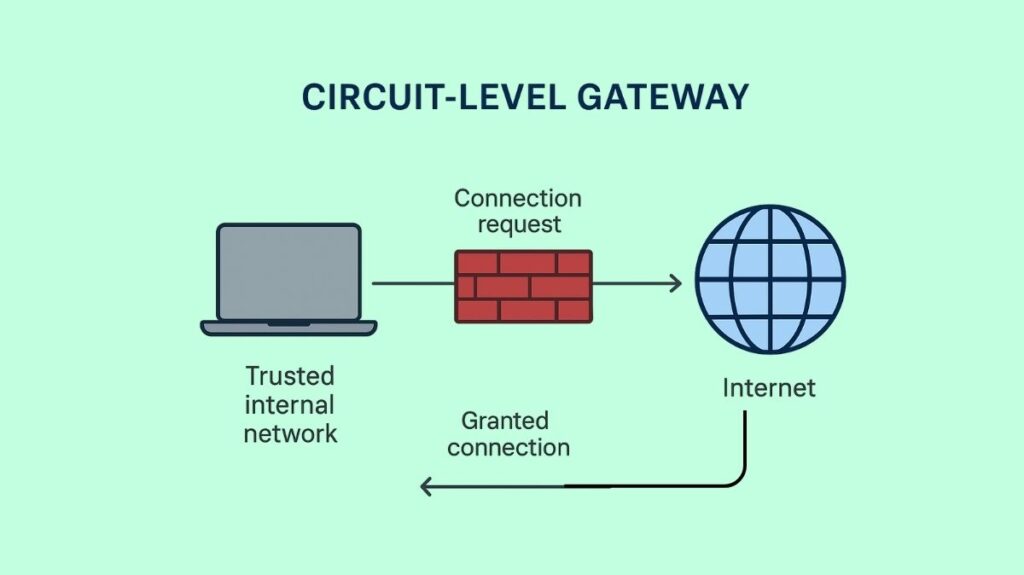
As a middleman, a CLG creates and maintains connections between an untrusted external network and a trusted internal network. In the TCP/IP stack, it functions as a “shim-layer” positioned between the application and transport layers.
TCP/IP Handshake Monitoring: The gateway examines the TCP handshaking procedure to confirm that a session initiation is legitimate and authorized. The three-way TCP handshake is used to verify that it complies with the security and privacy guidelines established by network administrators.
Proxy Functionality: The CLG serves as a proxy in place of permitting a direct connection. When a client sends a connection request, the gateway gets it, checks it against the rules for incoming or outgoing communication, and then connects the client to itself. After that, the gateway opens a fresh connection to the external server on the client’s behalf.
Virtual Circuit Establishment: The gateway establishes a virtual circuit or connection after the validity of the first session and a successful handshake. These two connections are then used to relay data.
Stateful Inspection: All open connections, including source and destination IP addresses, port numbers, protocols, and session timeouts, are tracked by the CLG through stateful inspection. Only when incoming packets meet the pre-established criteria for a legitimate session are they accepted after being compared to these records. When the firewall detects harmful activity in an incoming data packet, the connection is cut off. No more inspections at the packet level are carried out after a session has been approved. Upon terminating a session, the gateway closes the virtual circuit by deleting it from its session table.
You can also read What Is Syslog Server, How Does It Works And Syslog vs SNMP
Key Features
Session Layer Operation: At Layer 5 of the OSI model, the session layer operates by keeping an eye on TCP or UDP handshakes in order to manage and validate sessions.
Privacy Preservation: By concealing the IP addresses and other information about the internal network from outside hosts, the gateway makes it more difficult for hackers to target certain computers.
Stand-alone Security Functionality: A CLG can operate autonomously to offer Layer 5 network security by centralizing management and security guidelines for that layer.
Security Policy Enforcement: It makes sure that all sessions follow predetermined security requirements by setting criteria for session validation.
SOCKS Protocol Configurations: Socket Secure (SOCKS) protocol configurations can be used by CLGs as a client or proxy, enabling network hosts to access the public internet while maintaining security.
Reporting and Analysis: To assist administrators in evaluating security strategies and gaining knowledge of session activity, certain gateways provide reporting features.
Advantages of Circuit-Level Gateway
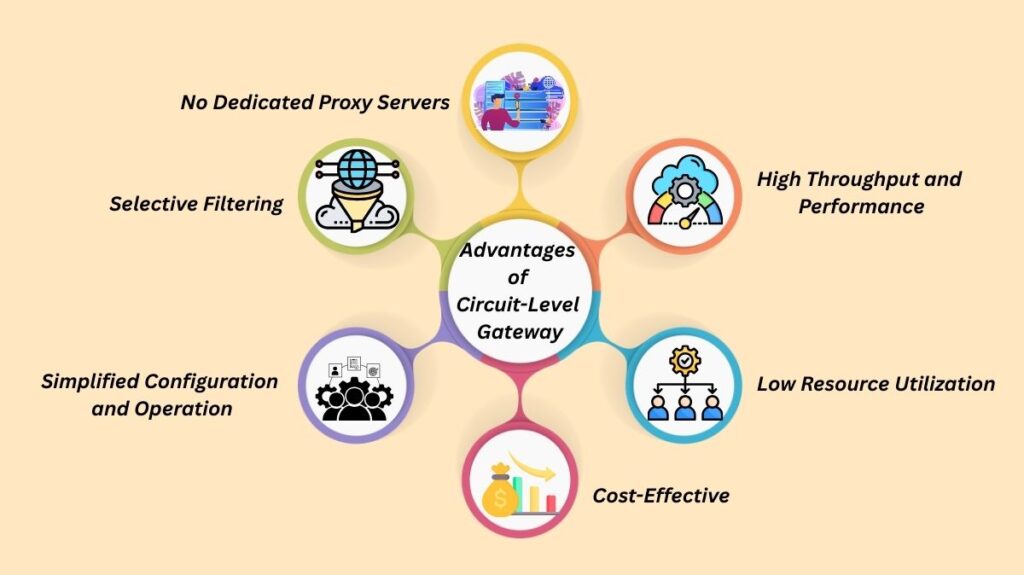
High Throughput and Performance: CLGs handle traffic rapidly and effectively by forgoing packet inspection, which results in high throughput with little effect on latency or network performance.
Low Resource Utilization: In comparison to firewalls that carry out in-depth packet inspection, they use fewer network resources.
Cost-Effective: When considering both software and hardware costs, CLGs are often low-cost and economical. Small and medium firms with tight budgets frequently choose them.
Simplified Configuration and Operation: They are easy to set up and maintain, concentrating on connection status instead of intricate protocols.
Selective Filtering: Source/destination addresses, ports, and other established connection criteria are the basis for selective filtering. When no complicated rule analysis is performed, it can quickly delete packets that have nothing to do with an established connection.
No Dedicated Proxy Servers: The absence of dedicated proxy servers makes network security administration easier because each application does not need its own proxy server.
You can also read Disadvantages Of Web Application Firewall And WAF Functions
Limitations and Disadvantages
Limited Inspection Capabilities: The main disadvantage is that CLGs are unable to examine the packets’ real data content. A malicious packet with a valid TCP handshake will be allowed to pass by the CLG, leaving the network open to assaults such as malware, viruses, or other malicious content concealed within a session that appears to be normal.
Lack of Awareness and Granular Control: CLGs only provide a simple pass-or-fail security check for the duration of the session and have no insight into applications or application data. Detecting assaults contained in packet content and defending against advanced application-layer attacks are beyond their capabilities. Advanced content filtering is also not something they provide.
Limited OSI Model Protection: They can only defend the OSI model Layer 5.
Compatibility and Configuration: CLGs work best with TCP connections, and their efficacy depends on the TCP/IP stack being configured correctly, which may call for vendor modifications.
No Traffic Monitoring (beyond handshakes): IN addition to confirming session handshakes, CLGs are unable to keep an eye on network traffic for questionable activity.
Frequent Update Requirements: CLGs may need to be updated frequently to remain effective against changing threats, which can demand a lot of IT staff resources.
Insufficient Data Leakage Protection: CLGs do not protect against internal network data leaks, although they do manage session integrity. As a result, extra security measures are required.
Overly Permissive: They can create any communication request that is allowed by the rules without checking for IP addresses or URLs that are known.
Adds Overhead (compared to simple packet filtering): Although effective, the session information inspection and proxy translation come with some extra costs.
When to Use a Circuit-Level Gateway
CLGs are frequently used in settings where efficiency and speed are critical, and quick session validation is required without incurring the processing expense of comprehensive packet inspection. They perform well for small and medium-sized businesses looking for an affordable solution to secure network sessions.
CLGs are rarely utilized as an independent remedy for all-encompassing network security, nonetheless. For Layers 3 and 4, they work best when paired with other, more sophisticated firewall technologies, like application-level firewalls (for Layer 7) and stateful inspection firewalls. Through the rapid reduction of the number of packets requiring longer, more in-depth examination, the CLG can enhance the performance of other security instruments in this layered security strategy.
Circuit Level Gateway Example
As part of their firewall solutions, Forcepoint (with their Stonesoft Next-Generation Firewall) and Juniper Networks (with their SSR120 network appliance) are two vendors that provide circuit-level gateway capabilities.
You can also read Comparison Of UTM Firewall Vs NGFW Next Generation Firewall
