Learn how a Web Application Firewall works to secure web applications. This guide details its crucial functions, while also addressing disadvantages Of Web Application Firewall like cost and management complexity.
CISCO Web Application Firewall
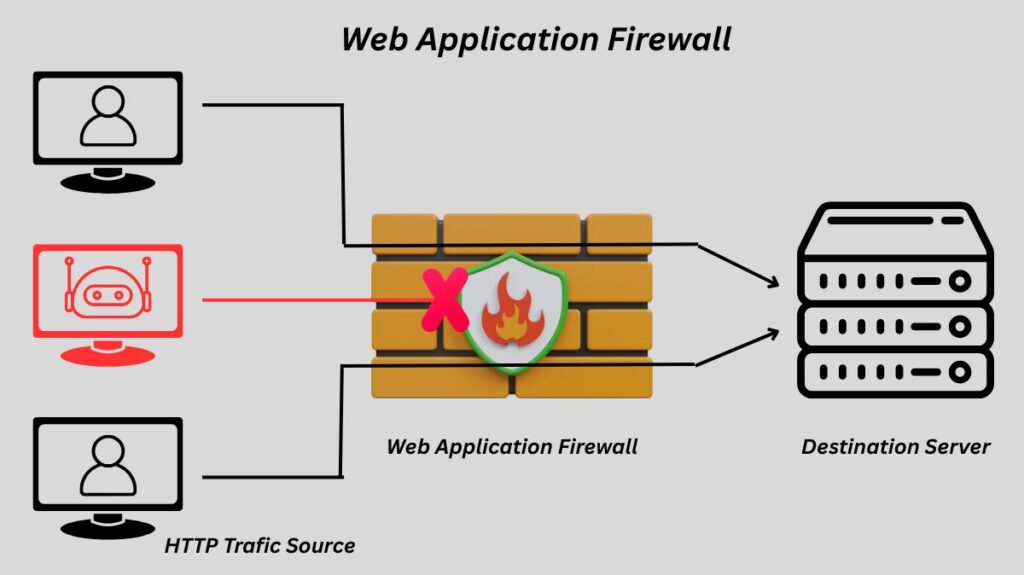
A Web Application Firewall (WAF) is a specialist security solution that filters, monitors, and blocks harmful HTTP/S traffic in order to secure web applications. In contrast to conventional network firewalls, which protect a network at lower layers, a WAF operates at the OSI model’s application layer (Layer 7) to particularly secure a web application. Another name for it is a proxy firewall or application layer gateway.
How Web Application Firewall Works
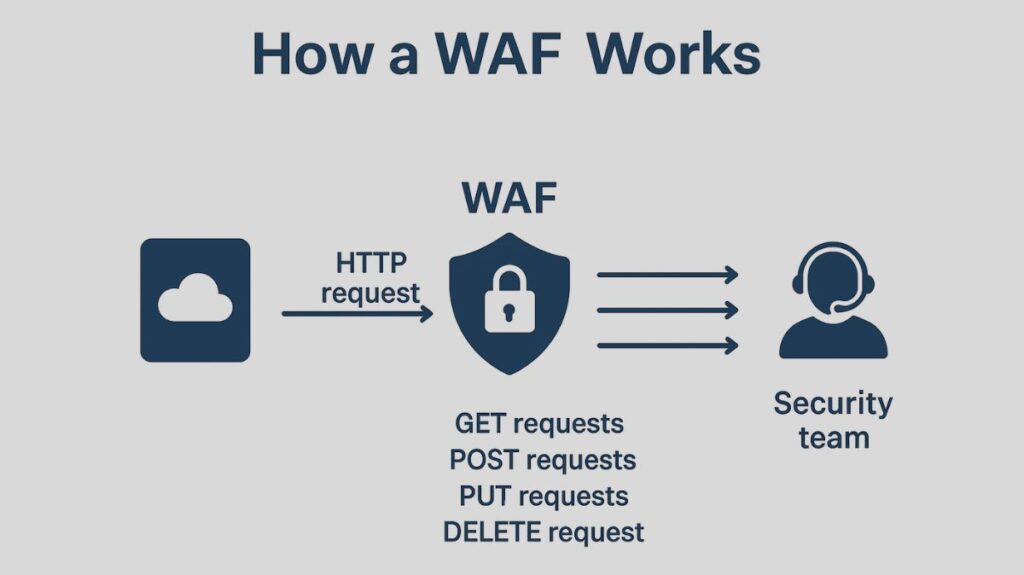
To find malicious traffic, a WAF examines HTTP requests and applies pre-established rules. A service, an equipment, or software could be involved. Key components of HTTP interactions that the WAF examines are as follows:
- GET requests: The server provides data in response to these requests.
- POST requests: The server receives data from these requests to alter its state.
- PUT requests: The server receives these requests for data creation or updates.
- DELETE requests: These are demands for data deletion.
For malicious patterns, the WAF also examines the HTTP request’s body, query strings, and headers. Should a match be discovered, the WAF will stop the request and notify the security team.
Functions of Web Application Firewall
WAFs carry out numerous vital tasks, including:
Deep Packet Inspection: To identify the particular program, they delve extensively into application layer data, protecting against attacks that take use of arbitrary or unusual port numbers.
URI/URL Filtering: Each web request’s Uniform Resource Identifiers (URIs), like URLs, can be examined by WAFs, which classify traffic before filtering or rate-limiting it according to pre-established rules.
Mitigation of Application Layer Attacks: WAFs play a critical role in identifying and stopping attacks that try to insert unauthorised content into authorised protocols or misuse application layer protocols.
Rule-Based Protection: WAFs are tailored with policies or guidelines to safeguard particular web applications.
Logging & Alerts: They keep an eye on traffic and send out alerts when they notice unusual activity.
Advanced Web Security Appliances: Advanced malware prevention, AVC, reporting, and the enforcement of acceptable usage policies can all be integrated into dedicated devices that can carry out malware scanning and URL blacklisting.
Next-Generation Firewall (NGFW) Feature: In addition to standard firewall functions, NGFWs carry out full packet reassembly and deep-packet inspection through Layer 7, with application layer inspection and URL filtering as key features.
You can also read Advantages And Disadvantages Of Packet Filtering Firewall
Security Models
WAFs determine what traffic is permitted or prohibited based on various security models:
Allowlist (Positive Security Model): By default, this architecture blocks all traffic and only permits specifically authorized traffic. Although exceedingly secure, it can be difficult to administer because each legitimate request needs to be whitelisted.
Blocklist (Negative Security Model): By default, this model permits all communication, but it rejects requests that contain any of a predetermined set of harmful signatures or patterns. It is simpler to put into practice, but it might not be immune to novel, unidentified threats.
Hybrid Security Model: Several WAFs provide complete protection by combining positive and negative security concepts.
Advantages of Web Application Firewall
Targeted Protection: Because typical network firewalls are unable to identify threats at the web application level, WAFs are specifically made to defend against them.
Proactive Security: By preventing traffic patterns that take advantage of zero-day vulnerabilities, they can defend against them even before a patch is made available. Newly identified vulnerabilities can be immediately fixed with a “virtual patch” provided by custom policies.
Compliance: By using a WAF, an organization can comply with standards such as PCI DSS (Payment Card Industry Data Security Standard), which requires that sensitive data be protected.
Mitigation of Application-Layer Attacks: When it comes to popular web threats, WAFs are quite successful against DDoS attacks, file inclusion, session hijacking, SQL Injection, Cross-Site Scripting (XSS), Cross-Site Request Forgery (CSRF), and bot traffic (such as web scrapers and credential stuffers). They provide protection for websites against the Top 10 OWASP vulnerabilities.
Enhanced Security without Code Changes: WAFs improve security to poorly constructed or outdated applications by adding a layer of protection without requiring modifications to the application code.
Tight Control and Detailed Logging: For security analytics and compliance, they offer extremely thorough logging capabilities along with extremely strict control over network traffic.
You can also read How Stateful Inspection Firewalls Works and Features
Disadvantages of Web Application Firewall
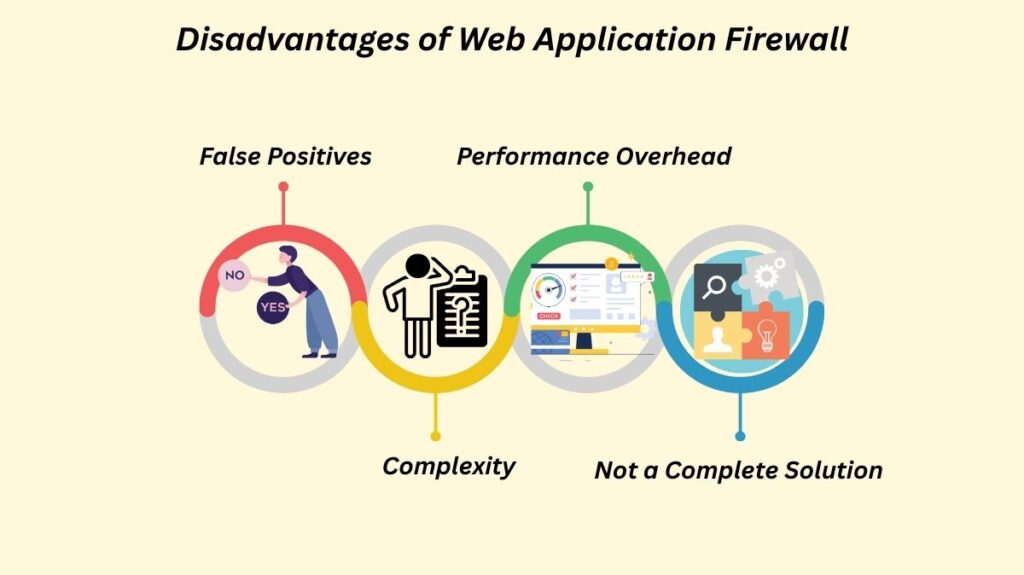
False Positives: WAFs frequently mistakenly label legal traffic as harmful and block it, which causes service interruptions for users.
Complexity: Security teams may find it difficult and time-consuming to manage and adjust a WAF’s rule sets.
Performance Overhead: Latency may be introduced by the thorough examination of each HTTP request, which could affect the web application’s performance.
Not a Complete Solution: WAFs are intended to be used in conjunction with other network perimeter security solutions, such as intrusion prevention systems and network firewalls, to create a comprehensive defence plan; they are not an absolute security solution. They are unable to defend against network layer attacks such as DDoS.
Deployment Options
WAFs can be used in a variety of ways.
Network-based (Hardware-based): These are often locally installed hardware appliances. Although they are the priciest solution and necessitate physical equipment storage and maintenance, they decrease latency. Their deployment options include reverse proxy, transparent bridge, and transparent reverse proxy.
Host-based (Software Solution): The software for an application has these software solutions completely integrated into it. Although they are less costly and provide greater customization than network-based WAFs, they nonetheless require deployment and maintenance expenses and use local server resources.
Cloud-based (Service): These are reasonably priced and simple to set up, usually requiring only a DNS change to reroute traffic. They are available as a subscription service. They are inexpensive up front, and the vendor regularly updates them to guard against emerging risks. Users cede control to a third party, though, and certain features might be “black box” features. AWS, Azure, and Kubernetes WAFs are cloud-based examples.
On-premises: A WAF appliance, either virtual or hardware, that is deployed in a company’s own data centre and is appropriate for customers that need high performance and flexibility.to counteract evolving bots.
Hybrid: Both on-premises and cloud-based solutions combined.
You can also read What Is Network Based Firewall, How It Works And Types
WAFs and Other Security Tools
WAFs are different from and a supplement to other security tools:
Network Firewalls: While WAFs concentrate on the application layer (Layer 7), they operate at lower layers (Layers 3 and 4) and safeguard the network itself.
Intrusion Prevention Systems (IPS): While a WAF focusses on protecting web applications at Layer 7, an IPS functions at Layers 3 and 4 and is usually signature-based.
Next-Generation Firewalls (NGFW): In addition to standard firewall operations, NGFWs are advanced firewalls that incorporate IPS and application layer capabilities. Two of NGFWs’ primary functions are URL filtering and application layer inspection.
Historical Context
With the rise in web server attacks in the late 1990s, dedicated WAFs were created. In order to make WAF technology more widely available, the open-source project ModSecurity was founded in 2002. Additionally, the OWASP Top 10 List, which was created in 2003, became a standard for web application security compliance that is at least covered by commercial WAF services. The market has expanded dramatically, particularly since the PCI DSS was created to prevent credit card fraud.
Protection Against Specific Vulnerabilities
Through the use of many detection techniques, WAFs guard against a variety of vulnerabilities, including those found in the OWASP Top 10:
- Signature-based detection: Identifies malicious communications by applying pre-established rules that match known attack patterns.
- Anomaly-based detection: Detects harmful traffic when it diverges from typical patterns of conduct.
- Machine learning: Identifies unknown harmful traffic using artificial intelligence.
Certain protection mechanisms are used by WAFs for particular attack categories:
- Broken user authentication: Employs token security.
- Excessive data exposure and security misconfigurations: Uses autolearning, 500 message replacement, and data masking.
- Broken access control: Uses IP and GEO policies, as well as API catalogue validation.
- Injection / Cross-Site Scripting (XSS): Validates API catalogues and applies both positive and negative security models.
- Malicious bots: Include behavioural analysis, device fingerprinting, and bot intelligence; certain WAFs also have deep learning bot detection systems.
You can also read Advantages And Disadvantages Of Next Generation Firewalls
