What is a virtual firewall?

Often called a cloud firewall or software firewall, a virtual firewall is a network security solution that runs in a virtualized environment and offers the same features as a conventional physical firewall but is built as software. It is intended to safeguard cloud environments and data centres’ virtualized architecture, which would be challenging to secure with traditional firewalls.
How Virtual Firewalls Work
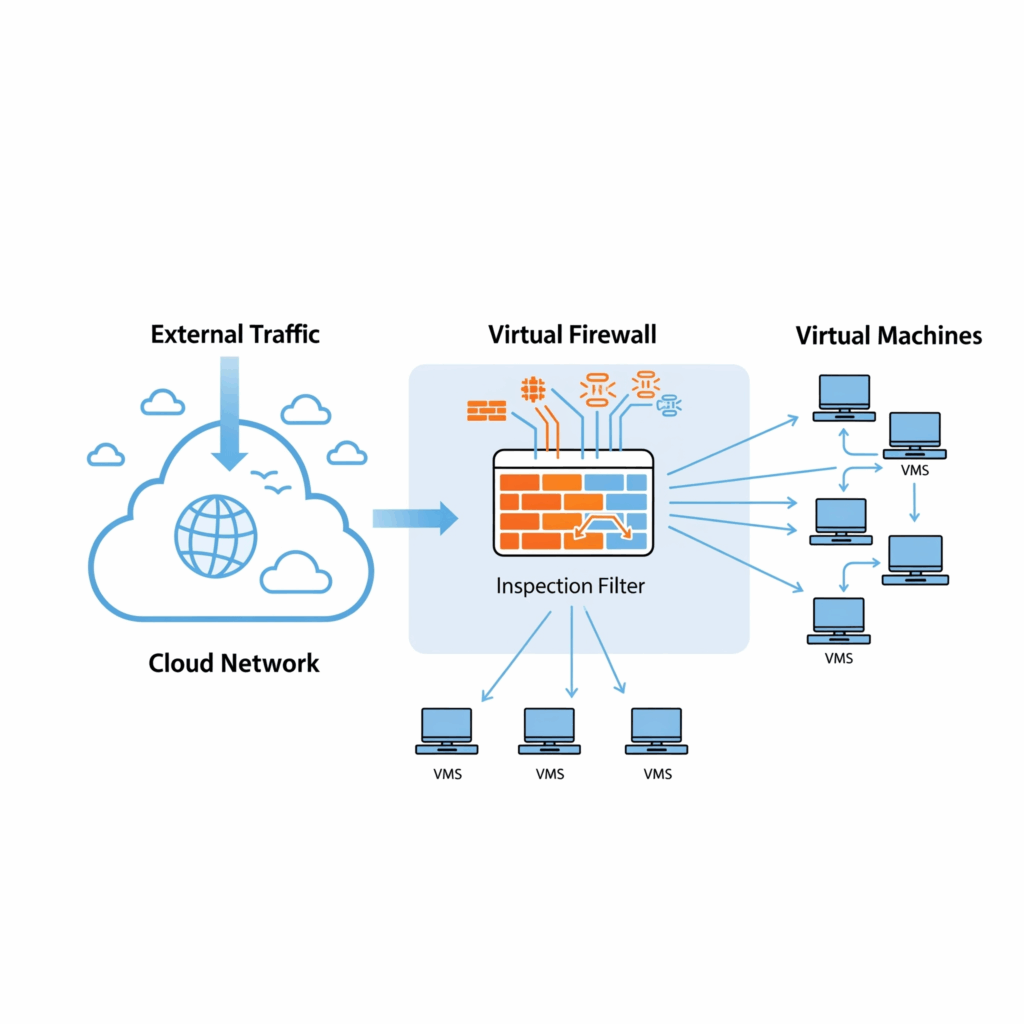
Virtual firewalls work by examining and managing network traffic flows between several zones of trust. A logical network segment with a specified security level is called a zone of trust. They function by:
Deployment: Virtual firewalls are deployed as software instances, often as virtual appliances or services. Hypervisors abstract a computer system’s physical resources to power them.
Traffic Interception: The virtual firewall intercepts network traffic entering or leaving VMs or moving east-west.
Security Policy Enforcement: The firewall enforces security policies on traffic, such as IP addresses, protocols, and ports. Following these principles, it may allow or deny access.
Packet Inspection: Virtual firewalls check packet headers for protocols, payload content, ports, source and destination IP addresses, and more. Many current virtual firewalls detect application-layer malware and other threats via DPI.
Traffic Management: Internal (east-west), inbound (north-south), and outgoing traffic are managed.
Reporting and Logging: Virtual firewalls log allowed and banned traffic, security events, and abnormalities. This data is useful for compliance, security analysis, and troubleshooting.
There are various ways that virtual firewalls can function:
Bridge-mode: In this mode, the virtual firewall functions similarly to its physical counterpart, intercepting traffic going to different network segments while positioned strategically (for example, as a bridge or inter-network virtual switch). It evaluates traffic coming into and going out of the virtualized environment or cloud.
Hypervisor-mode: In this mode, the virtual firewall is not a component of the virtual network, but rather resides inside the virtual machine monitor (hypervisor). Because it runs from within the kernel at native hardware speeds, it can be faster and capture all VM activity, including packet injections. Additionally, it offers isolation because people or software that is restricted to operating within a virtual machine cannot monitor or change its functioning.
Features of Virtual Firewalls
NGFWs address modern security challenges.
Threat Prevention
IPSs block DDoS, ransomware, phishing, and malware. They check every traffic for known dangers, independent of port, protocol, or encryption.
Attack Surface Reduction/Microsegmentation
Virtual firewalls limit cloud resource exposure by segmenting the network. Workloads are isolated and secured separately using microsegmentation, which also lowers the internal attack surface and contains threats.
Application Visibility and Control (AVC)/Application-Centric Security Policies
Application-Centric Security Policies, also known as Application Visibility and Control (AVC), are able to recognise and manage traffic based on people and applications as opposed to only IP addresses and ports. This makes it possible for security policies to be more flexible and granular.
URL Filtering
Using pre-established criteria or reputation ratings, they analyse URLs in web requests, classify them, and filter or rate-limit traffic.
Malware Prevention
This technique, which frequently includes real-time signature streaming, uses techniques like machine learning and dynamic analysis to identify and stop unknown file-based threats.
DNS Security
Uses machine learning and predictive analytics to stop attacks that take advantage of DNS.
IoT Security
Offers insight into unmanaged devices, identifies unusual conduct, and makes risk-based policy suggestions tailored to IoT settings.
Mobile Traffic Inspection
Protects mobile devices’ outgoing and incoming traffic.
Consolidated Security Management
Rich logging and reporting are provided by centralized management systems, which allow for the unified administration of virtual firewalls across several cloud deployments.
Also Read About What A Network Is And What Are Benefits Of Networking
Why Virtual Firewalls are Needed and Their Benefits
It is frequently not possible to secure dynamic cloud-based environments with traditional physical firewalls. Virtual firewalls alleviate these challenges and offer many benefits:
- Unlike traditional firewalls with limited capacity, they may scale up or down to meet changing network demands and cloud applications.
- Unlike physical firewalls, virtual firewalls show all internal cloud traffic, including east-west workload and container traffic.
- Security administration is simplified by their consistent security rules across cloud platforms or hybrid environments (public, private, and on-premises).
- Due to their low hardware, maintenance, and power costs, virtual firewalls are cheaper. Consumption typically determines licence.
- Software-based systems can be deployed quickly without hardware.
- Better East-West Security: They secure virtual computer traffic in the same cloud or data centre to prevent lateral attacks.
- Security Automation: Jenkins, Terraform, Ansible, and SaltStack automate DevOps provisioning and scaling.
- Many virtual firewalls support all major CSPs including AWS, Azure, GCP, OCI, and Alibaba Cloud, allowing unified management from one console.
- Application allow-listing and microsegmentation reduce attack surface and comply with GDPR and HIPAA.
Virtual Firewalls vs Physical
Both provide network security, however they differ:
Form Factor
Software-based virtual firewalls run on servers or hypervisors. Physical firewalls are established between environments or at the network edge.
Deployment
Cloud automation solutions enable rapid deployment of virtual firewalls, which are transferable between clouds. Professionals must install, wire, and configure physical firewalls.
Environment
Software-defined networks, cloud-based resources, and virtualized environments are all best protected by virtual firewalls. Local networks are shielded from outside threats by physical firewalls.
Insight
In virtualized environments, virtual firewalls offer complete insight into internal (east-west) traffic. This visibility might not be present in physical firewalls.
Cost
Because virtual firewalls do not require hardware, they typically offer reduced implementation and maintenance costs. The initial hardware expenditure for physical firewalls is usually larger.
Performance
Physical firewalls can respond to network perimeters more quickly because they are built to withstand higher traffic volumes. If not properly handled, virtual firewalls’ sharing of host resources may result in performance overhead.
Management
In hybrid and multi-cloud settings, virtual firewalls can be centrally managed. Installing and maintaining physical firewalls frequently calls for on-site IT personnel.
Deployment Scenarios and Examples
Common locations for virtual firewall deployments include:
- Public Cloud Deployments: Protecting information and programs housed on AWS, Azure, or GCP.
- Private Cloud Deployments: Protecting private cloud settings, which are frequently housed in specialized data facilities or on-site.
- Software-Defined Environments and Branch Locations: Protecting remote locations and branch offices connected by SDN or SD-WAN, deployed on SD-WAN appliances with integrated hypervisors.
- Cloud companies offer Infrastructure as a Service (IaaS) options for virtual firewalls to regulate network traffic.
Virtual firewalls include Fortinet FortiGate VM, Palo Alto Networks VM-Series, VMware NSX Firewall, Cisco Secure Firewall Threat Defence Virtual, Cisco ASAv, and Firepower Threat Defence Virtual. OPNSense, pfSense software, IPfire, Untangle NG Firewall, SmoothWall, UFW (uncomplicated firewall), CSF (ConfigServer Security), and Endian are a few free virtual firewall choices.
