Network Based firewall
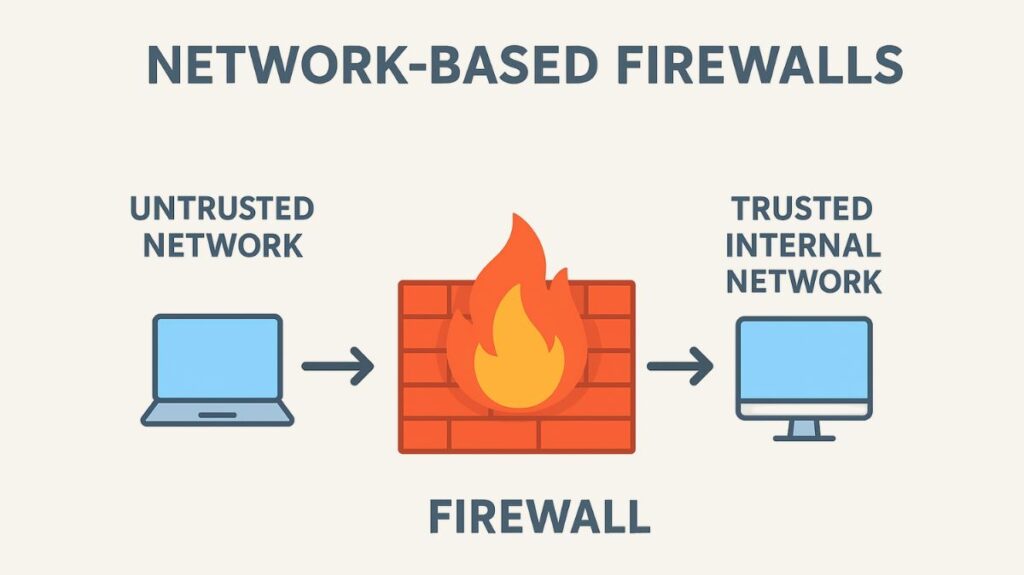
An untrusted external network, like the internet, is separated from a trusted internal network by a network based firewall, which is a security mechanism, hardware, or software. In order to prevent unauthorized access and only permit authorized traffic to flow through, its main function is to monitor and regulate all incoming and outgoing network traffic according to pre-established security standards. It is regarded as the network of an organization’s first line of defense.
How does Network Based Firewalls work
Network traffic monitoring, control, and protection are the functions of a firewall. It serves as a safeguard, keeping unwanted access to private digital infrastructures at bay through:
Traffic filtering: This procedure entails analyzing data packets coming into or going out of the network and determining whether to permit or prohibit them in accordance with pre-established security regulations. Firewalls do this using a variety of filtering methods:
IP address filtering: Incoming and outgoing packets are subject to source and destination IP address verification by the firewall. After comparing these addresses to a list of IP addresses that have been allowed or prohibited, it decides whether to allow or deny the traffic.
Packet filtering: The IP addresses and other data in the packet header, including port numbers, protocols, and packet kinds, are examined by this more sophisticated method. This gives you more precise control over network traffic by allowing or prohibiting particular services or apps.
Stateful inspection: The status of network connections is monitored by this procedure. In order to make better decisions regarding incoming packets based on their relationship to prior traffic, it keeps track of the context of each communication session in a state table.
Application-layer filtering: Often referred to as deep packet inspection, application-layer filtering looks at the data packets’ actual content instead than simply their headers. Because of this, the firewall is able to recognise and block particular protocols or apps, irrespective of their port.
Intrusion detection and prevention: Intrusion detection and prevention systems, or IDS/IPS, are also a common feature of contemporary firewalls. They detect and react to possible security risks instantly. Network address translation (NAT) to conceal internal network addresses from outside view and virtual private network (VPN) compatibility for safe remote access are other capabilities they might have.
Read more on NTP Server Configuration And How Does NTP Server Work?
Network Based firewall Functions and Features
A variety of features and functionalities are available through network-based firewalls to improve network security:
Traffic Control and Filtering: They analyze data packets and use pre-configured rules to decide whether to allow, stop, or discard communication. Both packet filtering (looking at packet headers) and IP address filtering are included in this.
Security Rules and Policy Enforcement: With the help of rules that administrators create to allow authorized communication and prevent unwanted access, firewalls carry out and enforce security and network policies. Having a “deny all” default policy that only permits traffic that is absolutely required is frequently a sign of a good security posture.
Network Address Translation (NAT): The internal IP addresses of network devices are concealed by many firewalls using NAT, which improves security and preserves IP addresses.
Virtual Private Networks (VPNs): Secure remote access to the network is made possible by firewalls’ ability to control VPN connections.
Deep Packet Inspection (DPI) and Application Awareness: Next-generation firewalls, or advanced firewalls, are able to examine the actual content of data packets (Layer 7) and recognize apps using application layer information, even if those applications utilize random ports.
Intrusion Prevention System (IPS): IPS functions are integrated into modern firewalls to detect and react to possible security threats instantly, preventing system hijacking and limiting access to network resources.
Access Control: By blocking unwanted devices or people from entering the network, firewalls enforce access privileges to preserve a secure network environment.
Logging and Monitoring: They record data transfers and network activities for analysis and threat detection, giving administrators useful information and enabling them to modify security settings.
Threat Prevention: By prohibiting unauthorized remote access attempts, stopping harmful file transfers, and refusing access to known malicious IP addresses, firewalls serve as an essential line of defense against a variety of cyberthreats, including malware, spyware, adware, and ransomware.
URL Filtering: Based on reputation scores, NGFWs are able to analyze and classify URLs in web requests and apply filtering or rate-limiting rules.
Stateful Filtering: This crucial function enables firewalls to monitor the “state” of a connection, retaining the context of every communication session and permitting only traffic that is a part of a session that has already been formed. This lessens the likelihood of Denial-of-Service (DoS) assaults.
Traffic Prioritization: Sensitive applications, like VoIP data, can have their traffic prioritized over email by modern Network Based firewalls to avoid communication delays.
Security Zones: Security zones are used by firewalls to specify which hosts are permitted to establish new connections, and rules are used to control traffic flow between these zones.
Read more on Key Difference Between Physical Server And Virtual Server
Types of Network Based Firewall
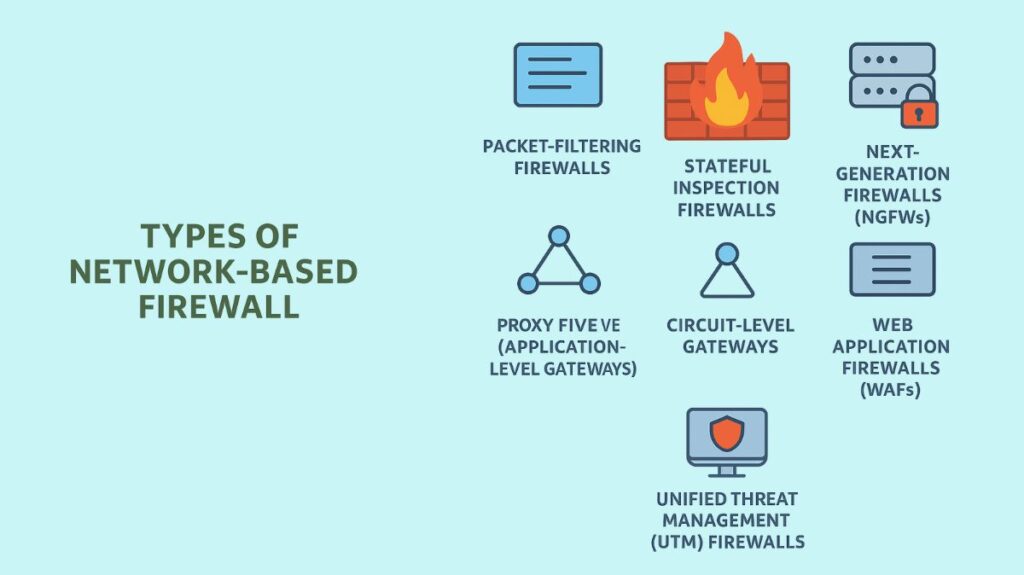
As they have developed, Network Based firewalls now provide varying degrees of security and functionality.
Packet-Filtering Firewalls: The simplest kind, which only examine the packet’s header (IP address and port number) and not its content. Although they are quick, they are easily circumvented.
Stateful Inspection Firewalls: These are more sophisticated than firewalls that only filter packets because they monitor the “state” of a connection. They are more secure because they keep track of all current connections and only permit traffic that is a part of a session that has already been set up.
Next-Generation Firewalls (NGFWs): The most sophisticated kind of firewalls, known as NGFWs, combine classic firewall operations with cutting-edge features including URL filtering, application-level control, intrusion prevention systems (IPS), contextual awareness, deep packet inspection, and enhanced malware protection. The Firepower and Cisco ASA product lines are two examples.
Proxy Firewalls (Application-Level Gateways): By establishing new connections and cutting off incoming ones, these serve as bridges between internal and external networks. With their deep packet inspection, content filtering, and internal network concealment, they offer excellent data security and privacy at the expense of somewhat slower performance.
Circuit-Level Gateways: Before permitting transmission, these secure connections or circuits, which operate at the session layer, confirm the legality of the session without looking at the contents of the packets.
Web Application Firewalls (WAFs): Created especially to guard against common web-based attacks on web applications by examining HTTP traffic and thwarting dangers like cross-site scripting (XSS) and SQL injection.
Unified Threat Management (UTM) Firewalls: Various security features, including as content filtering, intrusion prevention, antivirus, and occasionally VPN capabilities, are bundled into a single appliance.
Moreover, firewalls can be implemented as software programs (software firewalls) or as hardware devices (hardware firewalls).
Placement and Comparison to Host-Based Firewalls
Usually positioned at a network’s edge or perimeter, network-based firewalls serve as the first line of defense against outside threats. They can also be positioned at security borders between other network segments, such as safeguarding servers in a Remilitarized Zone (DMZ) that are reachable online.
On the other hand, software programs placed on specific network devices are known as host-based firewalls. Host-based firewalls offer a second layer of defense and endpoint security by giving precise control over the incoming and outgoing traffic of their particular host device, whereas Network Based firewalls safeguard the entire network perimeter. Combining host-based and network firewalls offers a multi-layered approach to network security.
Network Based firewall Benefits
Using a Network Based firewall has several advantages, including:
Protection Against Unauthorized Access: Preventing the entry of malware, hackers, and other bad actors into your network.
Reduced Risk of Data Breaches: Reducing the likelihood that private information may be lost, stolen, or compromised.
Control Over Network Usage: Enabling network resources, apps, and websites to be restricted by administrators.
Compliance with Security Regulations: Assisting companies in adhering to different security and compliance requirements.
Traffic Monitoring: Supplying thorough logs of network activities to spot possible security problems.
However, because of the thorough analysis they do on traffic, firewalls may create a small delay or latency. Adopting a “defense-in-depth” strategy is also essential because using just one firewall is insufficient; security should be introduced at almost every network location. It’s also critical that infrastructure and firewall devices be properly secured physically.
Misconfigurations, like having too lax rules or leaving default settings unaltered, are a frequent problem that can drastically lower a firewall’s efficacy. To prevent these problems, it is essential to conduct routine testing, monitoring, and adherence to the least privilege principle. Considerations for selecting a Network Based firewall should include affordability, scalability, performance, security features, ease of use, vendor support, integration with current infrastructure, and strong reporting and logging capabilities.
Read more on How Does A RADIUS Server Work, Architecture And Functions
