In this article, we learn about what Proxy Firewall is, how Proxy Firewall Works, Key Features of Proxy Firewalls, Advantages of Proxy Firewalls, Disadvantages, Challenges of Proxy Firewalls, Comparison with Other Firewall Types, and Proxy Firewall vs Packet Filtering.
Proxy Firewall
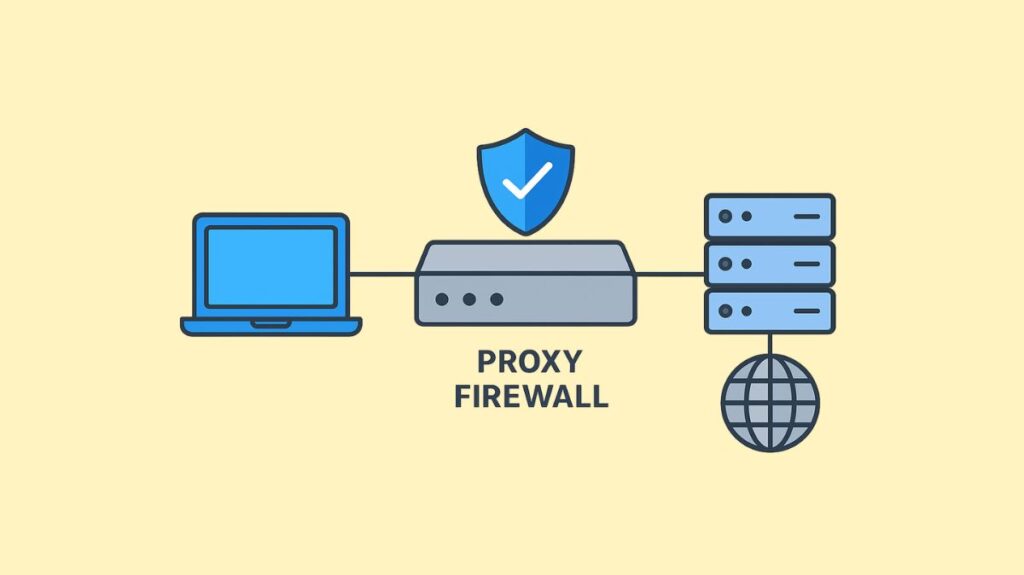
A network security tool called a proxy firewall, sometimes referred to as an Application-Level Gateway (ALG) or gateway firewall, serves as a safe bridge connecting clients on an internal network to external services. It is regarded as one of the safest firewall types.
How Proxy Firewall Works
By severing the direct link between the client and the destination server, a proxy firewall blocks direct traffic flow between the internal network and the external environment. One of its distinguishing features is this “go-between” procedure.
When a website or other external resource is desired by an internal user:
- A request is sent to the proxy firewall by the client.
- After receiving the request, the proxy firewall checks it against its security rules and cuts the connection.
- On behalf of the client, the proxy firewall establishes a new, distinct connection to the target server if the request is judged safe and allowed.
- In order to conceal the client’s internal IP address from the outside network, it then sends the request to the server from its own IP address. Only the proxy server’s IP address is visible to the target.
- After receiving a server response, the proxy firewall examines the data for malware and sends clean data to the client.
The OSI model places this procedure under Layer 7 application. It filters application layer protocols like SMTP, FTP, and HTTP.
You can also read Advantages And Disadvantages Of Next Generation Firewalls
Key Features of Proxy Firewalls
Intermediary Function: Serving as a gateway, they take in requests from internal users, process them, forward them to the external server, and then route the answers back through themselves.
Application Layer Inspection (Deep Packet Inspection – DPI): They perform a far more thorough examination than traditional firewalls because they analyze traffic at the application layer, looking for malicious code in the payload, or real content, of data packets. This enables threat identification and fine-grained control.
Hides Internal Network/IP Anonymity: By posing as internal devices, they protect user privacy by hiding internal IP addresses from the outside network, which makes it more difficult for hackers to map and target the network.
Content Inspection/Web Access Control: By blocking access to particular websites, detecting malicious material, blocking the download of dangerous files, or filtering traffic based on URLs or content categories, they can enforce security regulations and stop malware.
Traffic Caching: Web content that is regularly viewed can be locally cached by several proxy firewalls. This enhances network performance, decreases bandwidth consumption, increases reaction times, and improves performance.
Granular Control: They provide exact control over which protocols and applications are permitted and have the ability to impose user-level regulations.
Protocol Compliance: They can manage connection sequences and inspect protocols to make sure they adhere to set standards at various protocol stack tiers.
Malicious Data Detection: They can identify and stop harmful information (such as malware and phishing attempts) from getting to its target, which is another service offered by intrusion prevention systems (IPS).
Preventing Tunneling Attacks: When prohibited file transfers are concealed within permitted protocols, a practice known as malicious tunnelling, their application layer inspection capabilities can detect and stop it.
Logging and Auditing: All network activity can be logged by them, which offers useful data for auditing, troubleshooting, and security monitoring.
Integration with NAT: In order to conceal the user’s IP address, IP proxies frequently employ Network Address Translation (NAT) technology.
Advantages of Proxy Firewalls
High Security: Because of their extensive packet inspection and ability to block direct connections, they are regarded as the most secure kind of firewall.
Improved Privacy/Anonymity: They provide privacy and defend against external targeting and reconnaissance by masking internal IP addresses.
Advanced Threat Detection: Malware and phishing attacks are among the advanced cyberthreats that they can identify and stop by analyzing content at the application layer.
Network Performance Optimization: Content that is often visited can be cached to save bandwidth, speed up response times, and enhance network efficiency in general.
Granular Control: They enable stringent policy enforcement by providing incredibly fine-grained control over user access, protocols, and applications.
Secure Threat Analysis: Without jeopardizing internal network resources, they serve as a safe haven where threats can be examined and contained.
Disadvantages/Challenges of Proxy Firewalls
Performance Bottleneck/Impact: In high-volume traffic, terminating, evaluating, and re-establishing each connection can reduce network performance, cause latency, and bottleneck.
Complexity: Proxy firewalls require more expertise and ongoing maintenance than simpler firewalls. Vulnerabilities may be revealed by misconceptions.
Limited Protocol/Application Support: Some proxy firewalls may not support all network protocols or custom apps because they are made for particular protocols (like HTTP and FTP), which could be a drawback for particular processes or applications. Custom programs may need rewriting or exceptions to firewall policies.
Resource Intensive: They may require a lot of disc space and RAM.
Single Point of Failure: Proxy firewalls without fault tolerance can become single points of failure and block users from accessing network resources.
Encryption and Privacy Concerns: Data cached by proxy servers may reveal private information if it is not well protected. Ensuring encryption from beginning to conclusion is crucial. Communication from certain providers might not be sufficiently secured, leaving it open to decryption methods like SSL stripping.
Cost: Proxy server deployment and operation can be costly.
Possible to Disable: Proxy firewalls may be disabled by users in order to access content that is restricted, resulting in security flaws.
You can also read What Is Network Based Firewall, How It Works And Types
Types of Proxy Firewalls
Forward Proxy: The most widely used proxy firewall deployment is forward proxies. The external internet and local servers are connected using proxies in this configuration. Traffic cannot access the network until it has passed via the proxy server. Proxy firewall speeds can be increased and network loads can be controlled by caching traffic on the proxy.
Reverse Proxy: Firewalls that use reverse proxy reverse this configuration. In this instance, web content servers and the internet are separated by the proxy gateway firewall. Traffic moving out of content servers and onto private networks is filtered by the firewall. This enables owners of proxy servers to manage the data that private users receive and that exits their servers.
Web traffic load management is aided by reverse proxies. The proxy server allows content server owners to cache data. Content that users frequently view can be accessed fast without requiring them to send queries to the content server.
Transparent Proxy (Intercepting/Inline/Forced Proxy): In essence, transparent proxies also referred to as imposed firewalls are invisible to users. They can operate as forward or reverse firewalls, depending on the network’s requirements. It is difficult to detect this type of proxy since it does not change the formats of requests or responses. The flow of traffic appears normal to users.
By using transparent proxies, businesses can block specific content from external websites. Security personnel can also monitor user behaviour without fear of detection.
Non-Transparent Proxy: Non-transparent proxies need to be set up on the user’s machine (e.g., browser settings). The proxy is visible to the user and is capable of IP masking and content filtering.
Anonymous Proxy: An anonymous proxy conceals the user’s IP address from the online services they use, making their browsing activities untraceable.
High Anonymity Proxy (Elite Proxy): It is more difficult or impossible for the destination server to determine the use of a high anonymity proxy than an anonymous proxy because the former does not send the X-Forwarded-For HTTP header.
Distorting Proxy: Instead of hiding or masking the IP address, which can be done for security or privacy reasons, it gives the web service the wrong one.
Application Layer Proxy: It is responsible for the OSI model’s application layer. Incoming and outgoing network traffic is filtered at the application protocol level, and content translation and security are provided.
Circuit-Level Proxy: In the OSI model, the circuit-level proxy operates at the session layer. Two TCP connections are made: one with a device on the private network and one with a device on the external network. TCP segments are then often sent across connections by the proxy without examining the content.
Stateful Inspection Proxy: Inspection by the state Often called dynamic packet filtering firewalls, proxy firewalls keep track of each connection in a session table. Incoming packets can only reach internal servers if the connection is known and expected, which gives them a higher level of security than other kinds of proxy firewalls.
Deployment Scenarios
Forward Proxy, Reverse Proxy, Transparent Proxy, Transparent Bridge, and Traffic Mirroring are some of the forms of proxy firewalls that can be used. Bastion hosts, which are network devices with a high risk for attack and need comprehensive protection, are frequently where they are put.
Comparison with Other Firewall Types
Proxy Firewall vs. Traditional Firewalls
Operational Layer: At the application layer (Layer 7), proxy firewalls carry out in-depth content analysis. By filtering based on IP addresses and ports, traditional firewalls usually operate at the network or transport layer (Layer 3 and 4).
Direct Connection: By creating distinct connections, proxy firewalls stop direct communication. While they permit direct connections, traditional firewalls serve as filters.
IP Masking: Anonymity is provided via proxy firewalls, which conceal internal IP addresses. This is not a feature of conventional firewalls.
Inspection: Using proxy firewalls, extensive content inspection is carried out. Conventional firewalls typically do not perform as extensive an inspection of the data packet content.
Caching: Performance caching is a feature that proxy firewalls can provide. Traditional firewalls don’t have this.
Security Level: Proxy firewalls provide improved privacy and security for users. Conventional firewalls lack sophisticated content processing but offer a basic barrier.
Cost: Proxy firewalls typically cost more.
Proxy Firewall vs Packet Filtering
Inspection Depth: Proxy firewalls check the payload of every packet for harmful material. Packet filtering firewalls do not do a thorough content analysis; instead, they mostly analyze data packets at the network layer using IP addresses, port numbers, and protocols.
Resource Use: Firewalls using packet filtering require fewer resources and process data more quickly. Deep investigation of proxies necessitates greater computing power.
Proxy Firewall vs. Stateful Inspection Firewalls
Connection State: Proxy firewalls work by establishing a proxy connection and prohibiting direct communication. Stateful inspection firewalls track every session and check packet headers for continuity and state, keeping track of all active connections in a dynamic state table.
Inspection Focus: Proxy firewalls are quite good at detecting application-level exploits and deep data inspection. By keeping an eye on network traffic, stateful firewalls strike a balance between security and performance.
Proxy Firewall vs. Next-Generation Firewalls (NGFWs)
Approach: Proxy firewalls shield internal architecture from prying eyes. NGFWs merge advanced capabilities like application awareness, threat intelligence, and integrated intrusion prevention systems with more conventional firewall functions like stateful inspection.
Breadth: With threat intelligence, policy enforcement across applications, and deep packet payload inspection, NGFWs provide a more comprehensive and flexible approach to network security. Proxy firewalls stop packets from leaking through by concentrating on an application layer security barrier.
Integration with Other Security Tools
Several security technologies can be integrated with proxy firewalls to improve network security overall:
Intrusion Detection and Prevention Systems (IDPS): For real-time threat mitigation and the surveillance of suspicious activity.
Web Filtering and Content Filtering Solutions: To enforce rules and control website access.
Antivirus and Anti-malware Tools: To check traffic for harmful material before it enters the internal network.
Security Information and Event Management (SIEM) Systems: To combine logs and alarms in order to perform thorough security analysis and respond to incidents.
Data Loss Prevention (DLP) Solutions: To keep an eye on outgoing communications and stop illegal data transfers.
Virtual Private Network (VPN) Solutions: To encrypt traffic and authenticate users in order to enable safe remote access.
Network Access Control (NAC) Solutions: To make sure that devices trying to connect to the network are subject to security policies.
Load Balancers: In order to get the best possible speed and availability, traffic should be divided among several servers.
Identity and Access Management (IAM) Systems: In order to control user identities and implement user-based access restrictions.
You can also read Disadvantages Of Web Application Firewall And WAF Functions
